Land
Nagaland : Presentation of LaPaMS at DC Office, Dimapur
A presentation on the Web-based and open source-based Land Records Application Software, LaPaMs (Land Patta Management System) developed by NIC Assam State Centre under the supervision and guidance of Shri. Hemanta Kumar Saikia, Senior Technical Director, NIC, Assam was jointly organized by the District...
Haryana: Appointment Management System in Property Registration (AMS-HARIS) Project received Skoch Order of Merit Award 2014
Deed registration work is automated using the Haryana Registration Information System (HARIS) and Land Records management is being done using the Haryana Land Records Information System (HALRIS). To enhance the transparency in the deed registration work a new system of giving appointments...
Inauguration of Tehsil Computer Centre by Hon'ble Chief Minister, Himachal Pradesh
Hon’ble Chief Minister of Himachal Pradesh, Prof. Prem Kumar Dhumal inaugurated the Computer Centre of the newly created Tehsil of Tauni Devi in Hamirpur District on 1st September 2012. During the inaugural ceremony, Sh. I.D. Dhiman, Education Minister, Sh. Rajender Singh IAS, Deputy Commissioner,...
Hyderabad Urban Telangana Rising Hyderabad in e-Governance
NIC Hyderabad initiatives aim to create a digital ecosystem where opportunities abound for individuals and institutions alike. For citizens, this means improved access to essential services, simplified processes, and real-time grievance redressal. For the government, it translates to enhanced efficiency,...
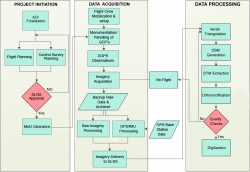
Use of Hybrid Survey Methodology and Bhu-Sarvekshan Software for Resurvey in Bihar
The Bihar state - spread over approx. 94163 sq. Km area, has an administrative setup comprising of 9 divisions, 38 districts, 101 subdivisions, 534 circles and 45,700 mauza(s) i.e. revenue villages. The very first survey of land i.e. Cadastral Survey (CS) of the state was conducted almost a century ago....




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


