News Update
Securing Machine Identities with Multi-Factor Authentication Enhancing Security and Compliance in a Perimeter-less Network Era
Multi-Factor Authentication (MFA) for machine identities adds an extra layer of security by requiring multiple verification methods during authentication. This helps protect against cyber threats by ensuring that only authorized machines can access systems and data. Implementing MFA for machine...
Cyber Risk Insurance Insurance Policy to cover financial liabilities arising from cyber incidents
Cyber Risk Insurance, also simply known as Cyber Insurance, is a kind of insurance policy which protects business houses as well as individuals from financial losses due to cyber-related incidents. These incidents include various forms of cyber-crimes such as data breaches and cyber-attacks. The...
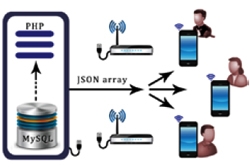
Case Hearing Status (CHS) Mobile App
The Android based CHS mobile App developed by NIC's Unit at Andaman & Nicobar is a modern and easy facilitation to access the daily cause list put up for case hearing procedure of the District and Sessions Courts of Port Blair. Now, the real time case progress status can be viewed through mobile...
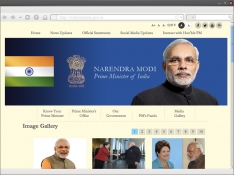
Launch of Prime Minister's Website
Just seconds after Shri Narendra Modi was sworn-in as the 15th Prime Minister of India, the official website of the Prime Minister of India http:// pmindia.nic.in/ was made live by NICs web development team with active support from NIC Cell at Prime Minister Office (PMO). Brimming with latest...
NATIONAL PORTAL OF INDIA 2.0: A Gateway to Government Information and Services
The India Portal (india.gov.in) is a Mission Mode Project under integrated services category of the National e-Governance Projects (NeGP) to bring in a Single-Windowaccess to Government information and services.




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


