Automation
Generative AI
Generative AI is experiencing unprecedented growth and adoption across diverse industries, fundamentally transforming organizational operations and the landscape of creativity and innovation. This technology, rooted in advanced machine learning algorithms, leverages vast datasets to autonomously generate...
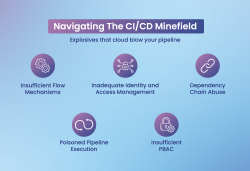
Securing CI/CD Pipelines Addressing the Unique Challenges in DevOps
CI/CD pipelines enable fast software delivery but come with security risks like weak flow control, IAM gaps, and dependency exploits. Mitigation includes role-based access control, multi-factor authentication, secure secrets management, and automated testing. Tools like Jenkins and GitLab CI/CD...
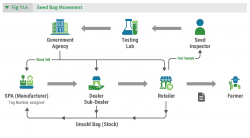
SATHI An ecosystem where each seed tells its own story
SATHI, or Seed Authentication, Traceability & Holistic Inventory, strives to create a nurturing digital environment. It aims to oversee seed production, ensure quality certification, and manage distribution with utmost care. The core objective is to offer complete traceability of seeds from their...
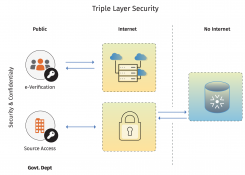
eCabinet - Automate Cabinet meetings in paper free and virtual mode
eCabinet/ eMantrimandal is a powerful software portal for State governments to conduct Cabinet meetings electronically and online mode. Developed by NIC, it maximizes usage of technology in meetings and reduces paper use. eCabinet automates work flow activities of meetings; before, during and after....
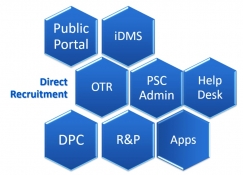
PSC-Soft Public Service Commission Software for Transformation
The PSC-Soft provides an integrated solution for the core functions of any State Public Service Commission with focus on providing user friendly interface for applicants with one-time registration facility. It is highlighted by the fact that during initial implementation stage in HPPSC, the...




 Subscribe
Subscribe

 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


