Automation
e-Counselling Services
e-Counselling services developed by NIC are the result of a focussed effort to put the best use of technology for bringing transparency in the admission process of the educational institutions in our country. This has also led to the implementation of a common selection process across...
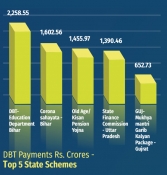
Direct Benefit Transfer - Supporting the financial Institution of the government during the crisis of COVID-19
Direct Benefit Transfer (DBT) plays an important role during the crisis times to provide sustenance to the highly effected population such as farmers, daily wagers, migrant labours etc. by transferring cash benefits directly to their bank accounts as well as delivering in-kind benefits such as...
Uttarakhand Teachers Eligibility Test (UTET) Online - Exam Management System-2019
Till 2018, the entire process UTET was carried out manually by the Uttarakhand School Education Board. Understanding the complications and challenges of the manual system, NIC- Uttarakhand proposed Department of School Education, Uttarakhand to design and develop a computerized system enabling automation...
Public Financial Management System : Facilitating digital inclusion and accelerating transformation to a Digital Economy
The Ministry of Finance has taken a big leap forward, with PFMS emerging as one of the largest financial management systems in the world, critical in bringing about transformational accountability and transparency in financial management and promoting good governance.
Anubhav Portal : A platform for retirees to cherish work life moments and help channelise enhancement in internal processes
Operated by the Department of Pension & Pensioners' Welfare under the Ministry of Personnel, Public Grievances & Pensions, Anubhav is the dream project of the Honorable Prime Minister. It provides a platform to retiring employees to share their experiences of working with the government...




 Subscribe
Subscribe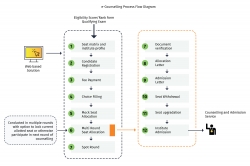




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


