Automation
ALFA - AUTOMATION OF LOCAL FUND AUDIT: BRINGING TRANSPARENCY IN INTERNAL AUDIT
The Automation of Local Fund Audit (ALFA) is to provide more fiscal discipline and efficiency in audit process. The launch of ALFA has brought in a more transparent, efficient and accurate Audit Process along with basic citizen services.
ICT in Public Distribution System
The primary policy objective of the Department of Food & Public Distribution (DoF&PD) is to ensure food security for the country through timely and efficient procurement and distribution of essential commodities across the country.This involves procurement of various food grains, building...
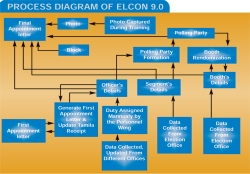
ELECON 9.0: Managing Assembly Elections in Bihar
Polling party formation, deployment of patrolling personnel, tagging of booths with the polling party, Electronic Voting Machines (EVM) randomization, vehicle allotment to the parties - all through random number techniques as per Election Commission of India (ECI) guidelines were made possible...
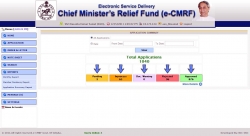
e-CMRF: Chief Minister's Relief Fund Automation at Odisha
e-CMRF is a web based application system has been implemented for the automation of Receipts & Issue of assistance under Chief Minister's Relief Fund (CMRF),to bring transparency & accountability at every level and promote timely assistance to the needy citizen.
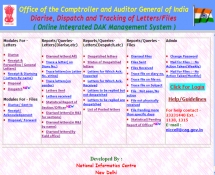
Online DAK Management System: Integrating CAG Office in a Smart Way
The Indian Audit and Accounts Department (IA&AD), 150 years old, with strength of more than 45000 employees in about 211 field offices located all over India and abroad is headed by the Comptroller and Auditor General of India (CAG) Office as the Head of Supreme Audit Institution of India....




 Subscribe
Subscribe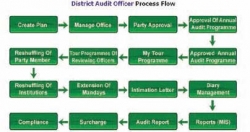

 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


