Automation
TEXTUAL & DEMOGRAPHIC DE-DUPLICATION OF LPG BENEFICIARIES
The subsidized domestic LPG connections in India are almost 14.58 crores. The policy to avail LPG gas connection is -One Kitchen, One Connection with Single bottle or double bottled cylinders for domestic purpose. Textual and Demographic Deduplication (TDD) technique assists in identifying...
AUTOMATION OF COMMERCIAL TAX DEPARTMENT, UTTARAKHAND
The Commercial Tax Department of Uttarakhand is one of the major contributors to the state revenue. It mainly interfaces with business community and is responsible for administering value added tax (VAT), central sales tax (CST), and State Tax on entry of goods into the local market. Its functioning...
HIMACHAL PRADESH- Setting New Paradigms in ICT
Proclaimed by ancient Indian texts as Devbhumi - Land of the Gods- the beautiful, far-flung Himachal Pradesh has an almost palpable presence of divinity and is famous for its abundant natural beauty. Himachal Pradesh has a rich culture which is very much apparent in the day to day lives...
HARIDWAR: Demystifying Haridwar with use of ICT
Haridwar, the paradise for nature lovers, presents a kaleidoscope of Indian culture and civilization. The word Haridwar or Hari-ka-dwar literally means Gateway to God. River Ganga, one of the major rivers of northern India, worshipped as a Goddess, runs through the district making Haridwar...
JHALAWAR: Leading ICT in the Land of Jhala Kings
The Princely State of Jhalawar was created in 1838 A.D. after being separated from Kota by the British. It got its name derived from Jhalas, the Jhala clan of Rajputs, also the rulers of Jhalawar. Lying in the south-eastern region of Rajasthan at the edge of the Malwa plateau, Jhalawar has rocky,...




 Subscribe
Subscribe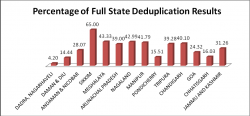





 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


