Technology
BLOCKCHAIN TECHNOLOGY : A mechanism revolutionizing multiple sectors, eliciting accountability and eliminating errors
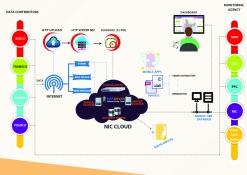
Since the blockchain database system provides security, trust, provenance, traceability and availability, the stakeholders of various business systems/ organizations can collaborate with each other. This technology has been initially experimented in the finance sector as in Bitcoin network, insurance...
First Technology Conclave of NIC held on 22nd and 23rd Januarary 2019
Profound discussions enabled knowledge sharing on harnessing advanced technologies and making India a digitally empowered nation.
Public Financial Management System : Facilitating digital inclusion and accelerating transformation to a Digital Economy
The Ministry of Finance has taken a big leap forward, with PFMS emerging as one of the largest financial management systems in the world, critical in bringing about transformational accountability and transparency in financial management and promoting good governance.
National Power Portal : Providing comprehensive framework for Power Sector data capture and dissemination
National Power Portal (NPP) is a unified system developed for Indian Power Sector to facilitate online data capture/ input (daily, monthly, annually) from generation, transmission and distribution utilities in the country and disseminate the power sector information (operational, capacity, demand,...
Anubhav Portal : A platform for retirees to cherish work life moments and help channelise enhancement in internal processes
Operated by the Department of Pension & Pensioners' Welfare under the Ministry of Personnel, Public Grievances & Pensions, Anubhav is the dream project of the Honorable Prime Minister. It provides a platform to retiring employees to share their experiences of working with the government...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


