Technology
API Management Solution at MyGov: Publish, manage, secure and analyze APIs in minutes
The API Management Solution deployed at MyGov facilitates the connection of data and business functions. MyGov uses Tyk as its API Gateway and API Dashboard.
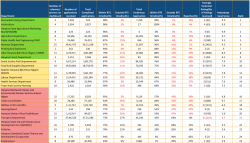
Antyodaya SARAL Haryana: A unified platform ensuring hassle-free & time-bound delivery and tracking of G2C services in the State
Having implemented Antyodaya SARAL, Haryana is the first state in the country to integrate so many schemes and services on one platform. The powerful solution developed by NIC Haryana has channelized the process of bringing about a fundamental behavioral change in the way the government functions, and...
eHRMS- Human Resource Management System: Digital platform for Personnel Management and Administration from 'hiring to retiring'
eHRMS is a step towards enhancing the efficacy and transparency of government organizations by focusing on their employees. This one of a kind application in the spectrum of e-Governance projects aims to harness the capabilities of ICT to improve the way HR processes are carried out. It has...
Software Project Execution Approach Workshop at NIC
National Informatics Centre (NIC), being the digital arm of the Government of India, has been immensely involved in the preparation of proposal, design, development, execution and maintenance/ support of various projects for the Central Government, State Government and District Administration.
Artificial Intelligence in e-Governance Applications : Extensive use of Machine Learning & Deep Learning
Artificial Intelligence development frameworks play a crucial role in enabling faster delivery of models built on them. They help provide data driven insights. Here, Machine Learning & Deep Learning Case Study is being considered for Object Detection, which may find an application in any...




 Subscribe
Subscribe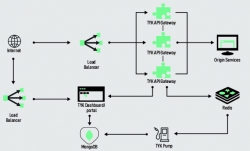




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


