Employment
e-Nijukti: Online System for Managing Job Oriented Skill Development & Training in Odisha
Employment & Technical Education and Training Department (ETET) was initiated by Government of Odisha with National Informatics Centre (NIC) serving as the knowledge partner to increase job opportunities and skill development in the state with the use of ICT. The online application (www. empmissionodisha.gov.in)...
e-Registration by Job Seekers in Manipur
The Employment Service, Manipur came into existence in 1957 and has been working closely with its Directorate of Employment as the controlling body for administration, establishment and financial supervision, under which there are nine District Employment Exchanges, Town Employment Exchanges and...
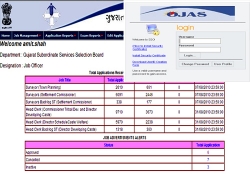
Online Job Application System for Government of Gujarat
Those who are looking for the jobs in Gujarat State government or thinking of making careers along with the various Gujarat Government departments, they can now apply through Online Job Application System.The vision of this online system is to devise an Information and Communication Technology (ICT)...
e-College*Suite: Integrated e-Governance solution for College Campus from NIC
In terms of public governance, India has been a laggard in the utilisation of ICT. There are several reasons for this. One is the monopolistic nature of public governance. It is the customer, in this case the "aam aadmi", who has to like or lump whatever is offered by the public institution....
Publishing of Exam Results & Counseling from Internet Data-Centre NIC
Internet Data-Centre at NIC (HQ) has been hub for e-governance activities be it a website, portal or e-gov project in providing a robust, reliable and secure platform for service delivery. Among the thousands of web/portals/e-gov projects hosted by NIC Data Centre, Electronic Publishing of Exam results...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


