Launch
Website of SDM (South) launched.
The website of the Sub Divisional Magistrate (South) office was formally inaugurated and launched by Deputy Commissioner, Chandigarh, Mr. Brijendra Singh on 06-11-09. SDM(S), Ms. Prerna Puri said that the website which can be viewed at http://chdsdmsouth.gov.in has been designed and developed by the...
Chief Minister, Himachal Pradesh launches the Department of Economics & Statistics website
Prof Prem Kumar Dhumal, Chief Minister of Himachal Pradesh, launched the website of the Department of Economics and Statistics. Addressing the media persons on the occasion, the Chief Minister informed that the website has weekly market rates available for all the Districts of Himachal Pradesh and that...
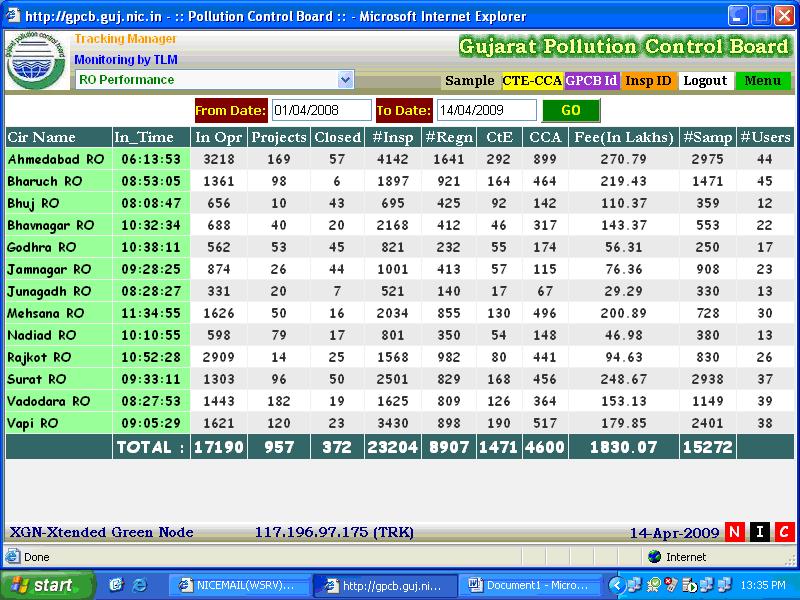
Gujarat Pollution Control Board goes online with XGN
"XGN has been developed by NIC-Gujarat State Centre for the Gujarat Pollution Control Board, facilitating the users in the day to day operations at 13 field offices in Districts, the Head Office & about 17000 Industries spread all over. XGN is in operation since June-2008 and has been instrumental in...
eSamadhan Portal launched by the Chief Minister of Himachal Pradesh
"Prof. Prem Kumar Dhumal, Chief Minister, Himachal Pradesh formally launched the eSamadhan (Online Public Grievance Redressal System) portal for State wide roll-out by allocating User IDs and Passwords to all Secretary level officers in Shimla. Speaking on the occasion, the Chief Minister stressed upon...
Andhra Pradesh Empowering through Innovation Driving Digital Transformation with IT
NIC Andhra Pradesh plays a pivotal role in delivering cuttingedge ICT solutions to the citizens doorsteps by harnessing emerging technologies. As the technological backbone of the state, the NIC AP State Centre seamlessly integrates advanced digital tools across government departments driving efficiency,...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


