Awards
GIGW wins Award in ICT
‘Guidelines for Indian government websites’ received the gold award in the ‘ICT’ category and ‘central government’ sector at the Skoch Digital Inclusion Awards 2012. The award was presented to the group by Mr Salman Khurshid, Hon’ble Minister, Ministry...
Online SPIDER Portal and eMANCHITRA selected for PC Quest Awards 2012
PC Quest, on its 25th anniversary has organised Best IT Implementation Awards, 2012. Out of 175 nominations from over 30 cities and 25 different types of industries, SPIDER and eMANCHITRA of Department of Planning, GoUP and NIC, Uttar Pradesh have cleared the second and third stage to be amongst the...
PRERANA - "Knowledge Stimulator" - Bagged eWorld-2012 Award for Best initiative in "Electronic Delivery of Services"
PRERANA – Post-Matric Scholarship REgistration Release And Network Automation, the e-Scholarship delivery mechanism for ST, SC, OBC / SEBC & Minority Department, Govt. of Odisha has received e-WORLD-2012 Award under Project Category “Best Initiative for Electronic Delivery of Services...
Apnakhata (LRC) Wins Award
eWORLD 2012 AWARDS LRC (Apnakhata) Shines Once Again NIC Rajasthan‘s LRC Apnakhata once again came out with flying colors. It bagged the prestigious eWorld Forum 2012 Public Choice Award under the under the Best ICT-enabled Rural Development Initiative of the Year recently under...
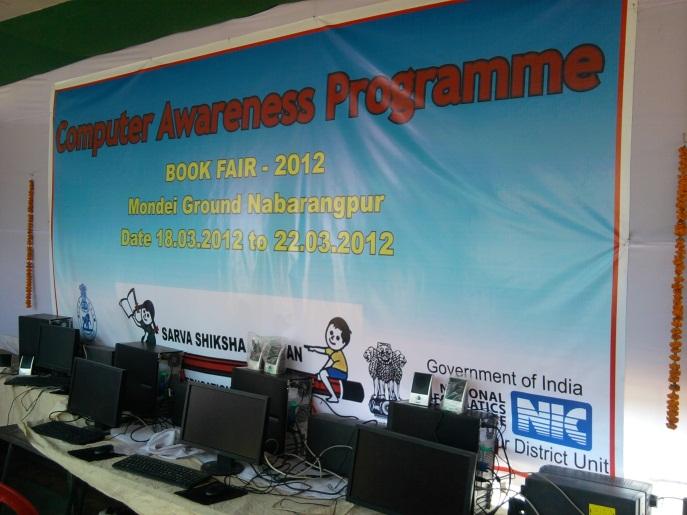
Free Computer Awareness Programme during BOOK FAIR 2012 Organized by District Administration & Sarva Sikhshya Abhiyan, Nabarangpur
A book fair was organized by District Administration & Sarva Sikhshya Abhiyan, Nabarangpur for 5 days at Nabarangpur District Headquarters. In the book fair one Free Computer Awareness Programme has been carried out by National Informatics Centre, District Unit, Nabarangpur for the children &...




 Subscribe
Subscribe


.jpg)

 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


