Free Computer Awareness Programme during BOOK FAIR 2012 Organized by District Administration & Sarva Sikhshya Abhiyan, Nabarangpur
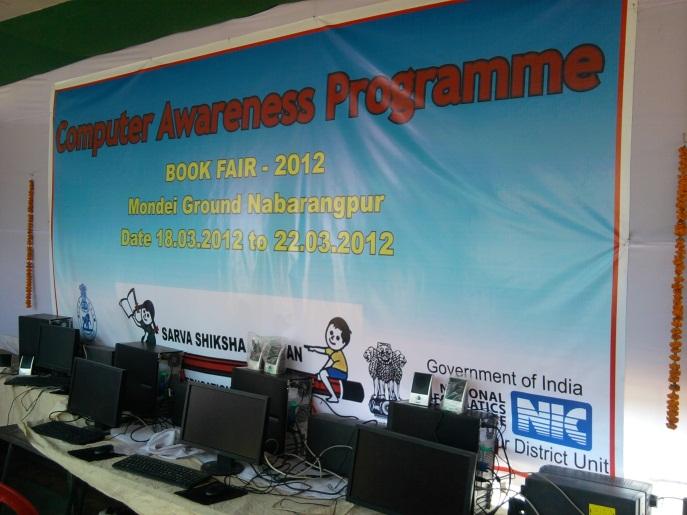

A book fair was organized by District Administration & Sarva Sikhshya Abhiyan, Nabarangpur for 5 days at Nabarangpur District Headquarters. In the book fair one Free Computer Awareness Programme has been carried out by National Informatics Centre, District Unit, Nabarangpur for the children & general public visiting the book fair. Organization of such a unique programme on Computer Awareness got the significant attention from School Children / General Public and other visitors of a tribal dominated district like Nabarangpur.
This Free Computer Awareness programme was open for visitors from 8 AM to 10 PM. In 5 days, more than 300 schoolchildren have registered. 8 School teachers from CAL (Computer Aided Learning) Schools have been sensitized to impart necessary assistance to the visitors. The awareness centre was setup in two cabins having a LAN of 8 computer systems and a printer. Internet was provided to the LAN using BSNL Broadband and USB Data Card.
Visitors were exposed on computer software, hardware, internet and websites & various e-Governance Projects / Initiatives of both State and Central Govt.
Shri Gyana Ranjan Misra, DIO & Shri Biswaranjan Bhukta, DIA have carried out the whole awareness programme including Sensitization of Trainers, LAN Setup and other necessary arrangements.
Reported by Shri Gyana Ranjan Misra, DIO, Nabarangpur




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


