Cyber Governance
Automation Initiatives & Transparency in eGovernance of Bihar
Shri Anand Kishor, IAS, is serving the Government at various key positions in Bihar such as Divisional Commissioner- Patna, IG-Prison, Chairman- Bihar School Examination Board and Director- Khuda Baksh Oriental Public Library. He has been successfully transforming innovative ideas into reality in partnership...
Telangana's Rashtriya Bal Swasthya Karyakram Software
This software captures various health conditions of children in the target age group. In cases where diseases are detected, or if medical intervention is required, support is provided free of cost and the parents of the affected children are informed through SMS automatically.
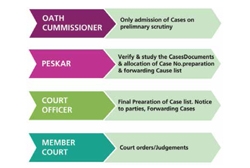
Revenue Court- Case Monitoring System of Odisha
Petitioners can now register a case online and track its status. Cause list is generated dynamically, which is published on the portal after approval by the competent authority. Hearing Notice is served online to the petitioner/ advocate and opponents by way of SMS, e-mail and physically through the...
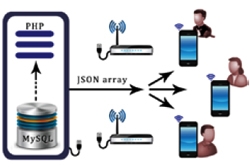
Case Hearing Status (CHS) Mobile App
The Android based CHS mobile App developed by NIC's Unit at Andaman & Nicobar is a modern and easy facilitation to access the daily cause list put up for case hearing procedure of the District and Sessions Courts of Port Blair. Now, the real time case progress status can be viewed through mobile...
Combating RANSOMWARE
Ransomware is a threat to Netizens, one that has become increasingly popular with criminals in the recent past. Combating this challenge requires not only the development of new technologies but also good Internet practices on the part of the users.




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


