Cyber Governance
Power Usage Efficiency In West Bengal State Data Centre
Data Centres consume a considerable amount of power for their smooth functioning and can cause significant loss of money and energy with lack of proper infrastructure management. Findings and strategies contextual to West Bengal State Data Centre for optimizing the utilization of power energy resources...
District Bhojpur, Bihar
District Bhojpur has been striding ahead in a progressive path of e-Governance since 1988 with the establishment of NIC Unit in the district. NIC continues to be instrumental in successfully implementing several ICT based initiatives. The achievements story continues.
District Namchi, Sikkim
NIC South District Unit of Namchi was established in the year 1993 and since then had a key role in promoting e-Governance in the District using Information and Communication Technology. Many software applications, websites and mobile apps have been developed and implemented with an objective to bring...
HP Telestroke Mobile App
The HP Telestroke, Android based Mobile App, developed for the citizens, 108 Ambulance personnel and Doctors is proving a boon to the Stroke patients in the State saving lives and educating the masses about the action to be taken in case of such a stroke.
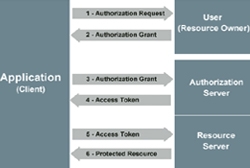
oAuth Based Single Sign-On
Introduction of oAuth 2.0 based Single Sign-On authentication mechanism in MyGov has enabled better user experience while accessing its various sites and Apps.




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


