Cyber Governance
Aadhaar Authentication Platform
The Authentication Services is integrated with 110 plus applications of States & Central Government Departments and Ministry with the monthly transaction of around 12 Crores in the month of November 2017. Indian Army, Public Distribution System, Digital Locker, CBSE, Jeevan Pramaan, Biometric...
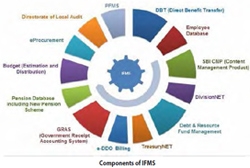
Strengthening Management of Finance In Meghalaya
With the computerization of online treasuries and other related activities using ICT, there has been a paradigm shift in e-Governance of Finance Department of Meghalaya. Most of services are now centralized and hosted at the dedicated servers, where citizen can access over the internet, hazzlefree.
Minister visits Shimla and Dharamshala
The Minister visits Shimla and Dharamshala, reviews ICT activities in the State, the role of National Informatics Centre and Common Service Centre
Ensuring Transparency and Reliability in Services provided to Citizens through Efficient ICT Solutions
NIC Punjab has successfully implemented various citizen focussed e-Governance projects in the State fulfilling the objective of making Government services available and accessible 24x7 to the common man at an affordable and hassle-free manner, at the same time ensuring efficiency, transparency...
Lsyncd (LIVE SYNCING DAEMON)
Lsyncd is a light-weight data replication tool which is free, easy to install and convenient to configure. It is an open source technology based, ultimate host to host replication or mirroring tool with very minimal configuration, cost effective and can assure the RPO in minutes or even seconds.




 Subscribe
Subscribe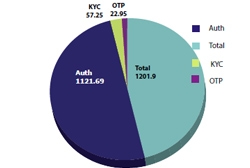



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


