Cyber Governance
Kendriya Vidyalaya Shaala Darpan
Kendriya Vidyalaya Shaala Darpan platform has been implemented by NICSI on NIC Clouds for 1185 Kendriya Vidyalayas across the country. A mammoth task was accomplished online in one of the largest school systems in the world with an estimated 1.2 million students and 50,000 teachers.
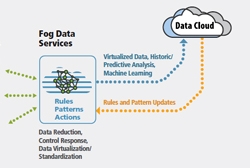
FOG Computing
Fog computing was introduced to meet objectives like improving efficiency and trim the amount of data to be transmitted for processing, analysis and storage, place the data close to the end user and finally provide security and compliance to the data transmission over cloud. Cloud is located up in the...
Bihar State ICT Initiatives:Soaring High With Excellence In m-Governance
NIC Bihar has been identified as a Mobile Competency Centre and has been involved with the design and development of several key Apps for various departments at a variety of levels of administration.
Union Minister Inaugurates Digital Government Research Centre (DGRC) in Patna
DGRC is a centre of excellence which strives to nurture, visualize and implement ideas in the field of eGovernance research and innovation
The National Meet on Grassroot Informatics
India has been making progress in the field of Information and Communication Technology with leaps and bounds. This progress, however, would not have been possible without the contributions of the officers closest to the ground reality, the District Informatics Officers (DIO).




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


