e-Services
e-HRM System for Government by NIC
This recently launched Application enables creation of e-Service book of employees from physical service book and automate the updation of e-Service book. This makes day-to-day processing of various records of employee possible, resulting in real time updation of servicebook and uniform implementation...
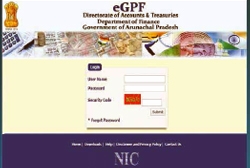
Online GPF System of Arunachal
Catering to the need of Directorate of Accounts and Treasuries by incorporating all the features required for maintaining GPF accounts and generating all essential reports and statements, the online GPF System follows a very transparent approach in providing a comprehensive resource of information...
Electronic-Human Resource Management System for Government Launched
Hon'ble Union Minister of State (Independent Charge) for Development of North Eastern Region (DoNER), PMO, Personnel, Public Grievances & Pensions, Atomic Energy and Space, Dr. Jitendra Singh launched the electronic-Human Resource Management System (e-HRMS) on 25th December,...
e-Labour Portal, CM Dashboard & NGDRS Launched in Punjab
Hon'ble Chief Minister of Punjab, Capt. Amarinder Singh recently inaugurated 3 important e-Governance initiatives in the State of Punjab. The e-Labour portal, Chief Minister's Dashboard and the National Generic Document Registration System (NGDRS) were the launched initiatives...
Arunachal Pradesh State - Transforming Challenges into Opportunities using Innovative ICT Advancements
Over the years, various ICT-based initiatives have been taken up by the Government of Arunachal Pradesh to foster innovation and improvement in the delivery of services to citizens, thereby making life simpler and easier. In the State, NIC does not leave any opportunities for innovations in order to...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


