Traffic
Online Rohtang Pass Permits Issuance System
To make it easier for the Rohtang Pass commuters, the payment gateway has been integrated with the system so that all the charges can be paid online and the permit is issued on successful receipt of payment by the Department. This web application is a unique mode of getting permits.
Online Consent Management and Monitoring System of JSPCB
Jharkhand State Pollution Control Board (JSPCB) has taken various initiatives during past year and a half, with the objective of 'Ease of Doing Business' in the State for transparent and expeditious decision making.
NATIONAL PORTAL OF INDIA 2.0: A Gateway to Government Information and Services
The India Portal (india.gov.in) is a Mission Mode Project under integrated services category of the National e-Governance Projects (NeGP) to bring in a Single-Windowaccess to Government information and services.
Muzaffarpur: A Major Hub for e-Governance in North Bihar
Muzaffarpur, a major town of north Bihar, situated on the Indo-Gangetic plain, has earned international encomiums for its delicious Shahi Litchi which are exported to other parts of the country and even abroad. Muzaffarpur has innumerable historical sites and monuments. There are a lot of Buddhist Viharas...
Palamu: Putting Digital Governance at the Forefront
Palamu- famous for its tiger reserve located at the Betla National Park just 25 Km from Daltonganj, the administrative headquarter of the district is situated on the banks of Koel river. The tiger reserve delights tourists with its scenic beauty is part of the nine tiger reserves of India under Project...




 Subscribe
Subscribe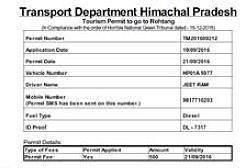




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


