Articles
Inaugurating the Awards ceremony, Honorable Union Minister, Shri Ravi Shankar Prasad felicitates winners
A National Awards Ceremony to honour the winners of the Hackathon was held at Stein Auditorium, India Habitat Centre, New Delhi on 1st November 2018. The awardees were felicitated by Shri Ravi Shankar Prasad, Honorable Minister of Law & Justice and Electronics & Information Technology, in the...
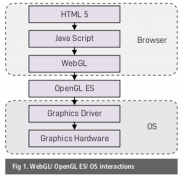
WEBGL AND THREE.JS : 2D/ 3D graphic rendering Javascript API
WebGL (Web Graphics Library) 1.0 is one of the Javascript APIs for rendering interactive 3D and 2D graphics within any compatible web browser without the use of plugins. There are many Javascript libraries that abstract WebGL and result in higher code level. One of the utility libraries is Three.js,...
Chatbot Framework for e-Gov : Meet VANI - Virtual Assistant of NIC
VANI is a virtual assistant that mimics a human & tries to help users - especially those not well versed with the web or technology in general. It is built using the principles of the latest disruptive technology of our times, that is Machine language & artificial Intelligence.
e-ABGARI - Complete IT Driven Supply Chain Management System for State Excise.
The project is built on the methodology of Reduced discretion - Electronic workflow - Electronic service delivery, adopting a web-enabled delivery mechanism to ensure the delivery of G2B, G2C, G2G services in a timely, transparent, more accessible and reliable manner.
Integrated Fertilizer Management System (urvarak.nic.in) : Ensuring Adequate & On-time delivery of Fertilizers to the deserving.
About 28.02 million tonnes of fertilizers were sold during April-September of this fiscal year through the PoS devices installed at retail shops under the Direct Benefit Transfer (DBT) scheme. Paperless processing of weekly subsidy claims and payment to companies through PFMS is fully operational now.




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


