Articles
Online Examination System of NIC (OESNIC) : Boasting of a robust architecture enabling the simultaneous operation of multiple exams
OESNIC has replaced the existing examinations, conducted using paper, with online paperless system in government departments and schools, thereby ensuring 100% transparency in conducting examinations and mark sheet evaluation. Till date, more than 60 examinations have been conducted for NIC...
Public Financial Management System : Facilitating digital inclusion and accelerating transformation to a Digital Economy
The Ministry of Finance has taken a big leap forward, with PFMS emerging as one of the largest financial management systems in the world, critical in bringing about transformational accountability and transparency in financial management and promoting good governance.
District Mahabubnagar, Telangana : Setting new horizons towards digital empowerment and enhanced e-Governance
NIC Mahabubnagar District Centre has been spearheading the implementation of ICT services in the District with great zeal, thereby helping the District Authorities establish a better connection with citizens. A number of projects, speeding up e-Governance in the District, have also helped citizens...
GOA STATE : On a progressive path to become the next IT Hub of India
NIC Goa State Centre is the leading solution provider of ICT services in the State. Aimed at better e-Governance, the initiatives by NIC Goa have earned several prestigious accolades to its credit. South Goa is a unique District in India where a complete Data Centre is provided by the District Magistrate.
DG NIC interacts with Senior NIC Officers on New Year Day
The year begins on a significant note with launch of standardised NIC Logo. New Year is the time to reassure commitment to attaining future goals while cherishing the past accomplishments. As 2019 rolled in, Dr. Neeta Verma, Director General, National Informatics Centre (NIC), convened a meeting...




 Subscribe
Subscribe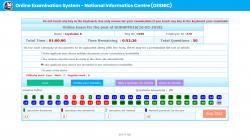





 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


