Articles
District Kurukshetra, Haryana : Promoting the vision of Digital India and raising the bar for e-Governance
Marking an active contribution to the aim of Digital India, NIC Kurukshetra District Centre has devised and implemented technological solutions to help enhance e-Governance, thereby addressing social needs of citizens. Community engagement has also been an area of constant focus for the District...
District Koraput, Odisha : Speeding up e-Governance through ICT-enabled initiatives
NIC Koraput has been playing a vital role in making the District a leading one in terms of providing ICT-enabled government services to citizens. DARPAN is a major project implemented for District Magistrate to monitor the execution of schemes on real time basis, while Geographical Information System...
MADHYA PRADESH : Pacing up with technological advancement to lead ICT transformation for efficient e-Governance
NIC Madhya Pradesh, The Cyber Gateway of the State, was set up in Bhopal in 1988 to play a catalytic role in promoting informatics culture and providing ICT services to Government Departments and Organizations. The roads from rich historical past are passing by the present developing State...
Anubhav Portal : A platform for retirees to cherish work life moments and help channelise enhancement in internal processes
Operated by the Department of Pension & Pensioners' Welfare under the Ministry of Personnel, Public Grievances & Pensions, Anubhav is the dream project of the Honorable Prime Minister. It provides a platform to retiring employees to share their experiences of working with the government...
National Power Portal : Providing comprehensive framework for Power Sector data capture and dissemination
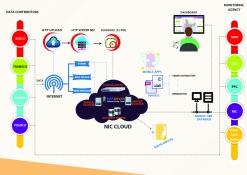
National Power Portal (NPP) is a unified system developed for Indian Power Sector to facilitate online data capture/ input (daily, monthly, annually) from generation, transmission and distribution utilities in the country and disseminate the power sector information (operational, capacity, demand,...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


