Articles
BLOCKCHAIN TECHNOLOGY : A mechanism revolutionizing multiple sectors, eliciting accountability and eliminating errors
Since the blockchain database system provides security, trust, provenance, traceability and availability, the stakeholders of various business systems/ organizations can collaborate with each other. This technology has been initially experimented in the finance sector as in Bitcoin network, insurance...
Artificial Intelligence in e-Governance Applications : Extensive use of Machine Learning & Deep Learning
Artificial Intelligence development frameworks play a crucial role in enabling faster delivery of models built on them. They help provide data driven insights. Here, Machine Learning & Deep Learning Case Study is being considered for Object Detection, which may find an application in any...
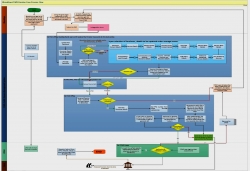
eNirvachan : An online Polling Personnel Management System for Election Department of Assam
e-Nirvachan (Assam) is a solution product developed by NIC Assam for the management of election processes. It can be used for any election, be it parliamentary or assembly or any state level (Panchayat/Council) election. Initially, in order to ease the processes of manpower management for an election,...
PFMS-Pension (e-PPO) : Enabling digitally signed PPO and seamless vouching of post-retirement benefits electronically to pensioners
PFMS-Pension is a web application developed by NIC Controller General of Accounts (CGA) for the generation of digitally signed Pension Payment Orders (PPOs) and vouching of post-retirement benefits to pensioners through electronic mode, incorporating Central Civil Services Pension Rules.
District Vellore, Tamil Nadu : On a high ride to leverage e-Governance through ICT initiatives
Vellore is one of the thirty two Districts of the enchanting Tamil Nadu State. NIC Vellore was established here to provide ICT support to District Administration and other Departments to facilitate efficient e-Governance in this large area bound District. Equipped with state-of-the-art IT infrastructure,...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


