Articles
Integrated Financial Management System (IFMS) An end-to-end system for Financial Management in the Government of Kerala
NIC Kerala has developed and implemented various application modules in the IFMS Project. As part of the IFMS project, smooth and successful integration has been achieved with various stakeholder applications such as SPARK (HR Management System) and EMLI (Effective Management of Letter of Credit Issuances).
Software Project Execution Approach Workshop at NIC
National Informatics Centre (NIC), being the digital arm of the Government of India, has been immensely involved in the preparation of proposal, design, development, execution and maintenance/ support of various projects for the Central Government, State Government and District Administration.
eCourts Services : Transforming Judiciary for Effective Justice Delivery
eCourts, a Mission Mode Project of the Government of India, has set an example of successful eGovernance project reaping rich dividends to litigants and citizens of the country. The eCourts project was conceptualized on the basis of the National Policy and Action Plan for Implementation of Information...
Gems of Digital India Awards 2018
Coeus Age Consulting who have been promoting and encouraging e-Governance initiatives through their Gems of Digital India Awards since 2017, unveiled the 51 Gems of Digital India, 2018 in a glittering ceremony at the Hotel Shangri La- Eros, New Delhi on 13th June 2018. The discovery of the Gems...
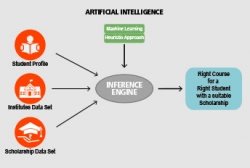
Right course for a right student With a suitable scholarship too : an AI approach
The possibilities are endless with the development of Artificial Intelligence based tool which can help and guide the students in selecting the suitable branch of higher studies in their area of interest to achieve their career objective.




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


