Articles
Hamirpur: ICT in the Veer Bhoomi
Hamirpur district, the Veer Bhoomi is one of the twelve districts of Himachal Pradesh. The tract is hilly covered by Shivalik range. The elevation varies from 400 meters to 1100 meters. The district is well connected by roads from all sides. Hamirpur is the most Literate district in Himachal Pradesh....
Hands free Computing by Integrating Speech Recognisation
Voice reorganization and text to speech system is becoming a powerful tool to provide the services through ICT for the physically handicapped people. While entering to ATM counters and just after swapping the ATM card in the reader, a greeting voice as well as guiding instruction can be heard in almost...
SSL VPN: A Technology Overview
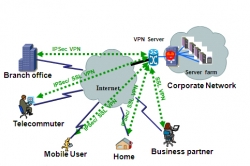
In the world of distributed computing, corporate applications are hosted in data centers located in multiple locations and are accessed by many users from various locations. To provide secure access to such network resources, technocrats have designed Secure Socket Layer Virtual Private Network (SSL...
e-Procurement: Bridging Digital Divide
An Exclusive Interview with Sh. Pradipta Kumar Mohapatra, IAS, IT Secretary, Govt. of Orissa on successful completion of one year of Implementation of NIC-GeP in Orissa
Orissa: Bringing Transparency in Governance
Orissa, a land of quintessential charm, with its natural bounties, gracefully blends the old world splendour with the modern day developments. While nature abounds in all its glory with unspoilt and alluring beaches, rivers, lakes, waterfalls, hills, forests, wildlife and a tribal culture, which is still...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


