News
SMS based Complain Monitoring System for Tripura Police
SMS based complain Monitoring System for Tripura Police was Inaugurated by Hon'ble Chief Minister of Tripura on 3rd January 2011. SMS being apowerful personal communication channel , wherever there is need or benifit for sharing information, specifically, the government organisation can leverage...
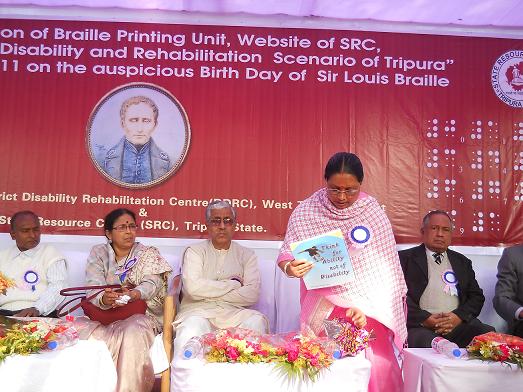
Service towards the Disbaled Persons of Tripura
Hon'ble Chief Minister of Tripura Shri Manik Sarkar inaugurated the website of State Resource Centre of the Disabled Person on 4th January 2011. Often due to lack of consolidated information Disabled person have been deprived of Government assistance. Under the able direction and guidance of...
Initiatives to improve service delivery to GPF subscribers
To improve the service delivery to GPF subscribers Interactive Voice Response System (IVRS) and Website were launched in January 2009. Through IVRS subscribers can access information such as Opening Balance, Closing Balance, Current Balance, Advance details etc. over phone. ...
Haryana Wakf Board goes on-line
On Monday, the February 7, 2011, Shri Vivek Mehrotra, IAS, Secretary, Ministry of Minority Affairs, Govt. of India (MoMA) inaugurated the Centralized Computing Facility (CCF) established at Haryana Wakf Board, Ambala (HWB) under the Project “Computerization of Records of the State Waqf Boardsâ€...
GIGW Workshop
Orientation Cum Training Programme on GIGW Held A two day comprehensive workshop of NIC officials on GIGW (Guidelines for Indian Government websites) was held on the 19-20th Jan. 2011 at Secretariat Jaipur. More than seventy NIC officer's from the district and the state unit...




 Subscribe
Subscribe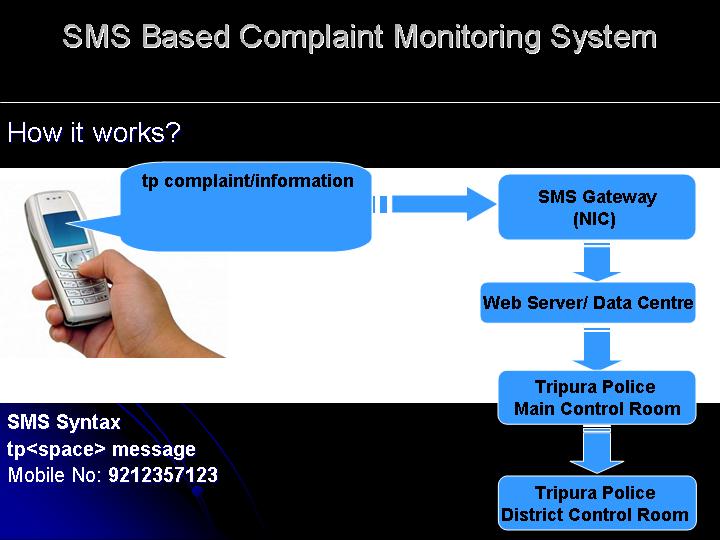



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


