News
Sh. Gurudas Kamat, Hon ble Min. of State for Home Affairs and Comm. and IT, Govt. of India launched Mobile Money Transfer Service on through NIC s VC
Sh. Gurudas Kamat Hon ble Minister of State for Home, Communication andIT launched Mobile Money Transfer Service of Department of Post at Chandigarh on 1st June 2011. CPMG Patna, Bihar also participated through Video Conferencing. NIC, Punjab and VC, Division NIC-Hq extended support to...
Haryana: Visit of Standing Parliamentary Committee on Rural Development
The Standing Parliamentary Committee on Rural Development comprised of the following Members of Parliament: 1. Smt. Sumitra Mahajan of Madhya Pradesh – Chairperson 2. Dr Pulin Bihari Basske of West Bengal 3. ...
Refresher Course on “Technological Aspects†Held
Refresher Course on “Technological Aspects” Held A five days refresher programme on "Technological Aspects" of various projects was held at NIC, District Centre, Pratapgarh (Raj) from 2nd- 6th May 2011. The second in the series of such programmes...
A State-wide Review-cum-Orientation Programme through VC on MCTS Application in the state of Orissa on 24th May 2011
A State Level Review-cum-Orientation Programme on MCTS (Mother and Child Tracking System); a system of name-based tracking of pregnant mothers and children for better coverage of ANC, institutional delivery and immunization; was organized through multipoint-VC on 24th May 2011 in which all the 30...
GePNIC Presentation at Eastern Coalfields Limited (ECL), Asansol, WB
Inspired by the success story of Mahanadi Coalfields Ltd. (MCL), Sambalpur, Orissa, Eastern Coalfields Limited (ECL), Asansol, WB, a premier subsidiary of Coal India Limited, under the Ministry of Coal, Govt of India, has shown interest for implementation of NIC e-Procurement System. ...




 Subscribe
Subscribe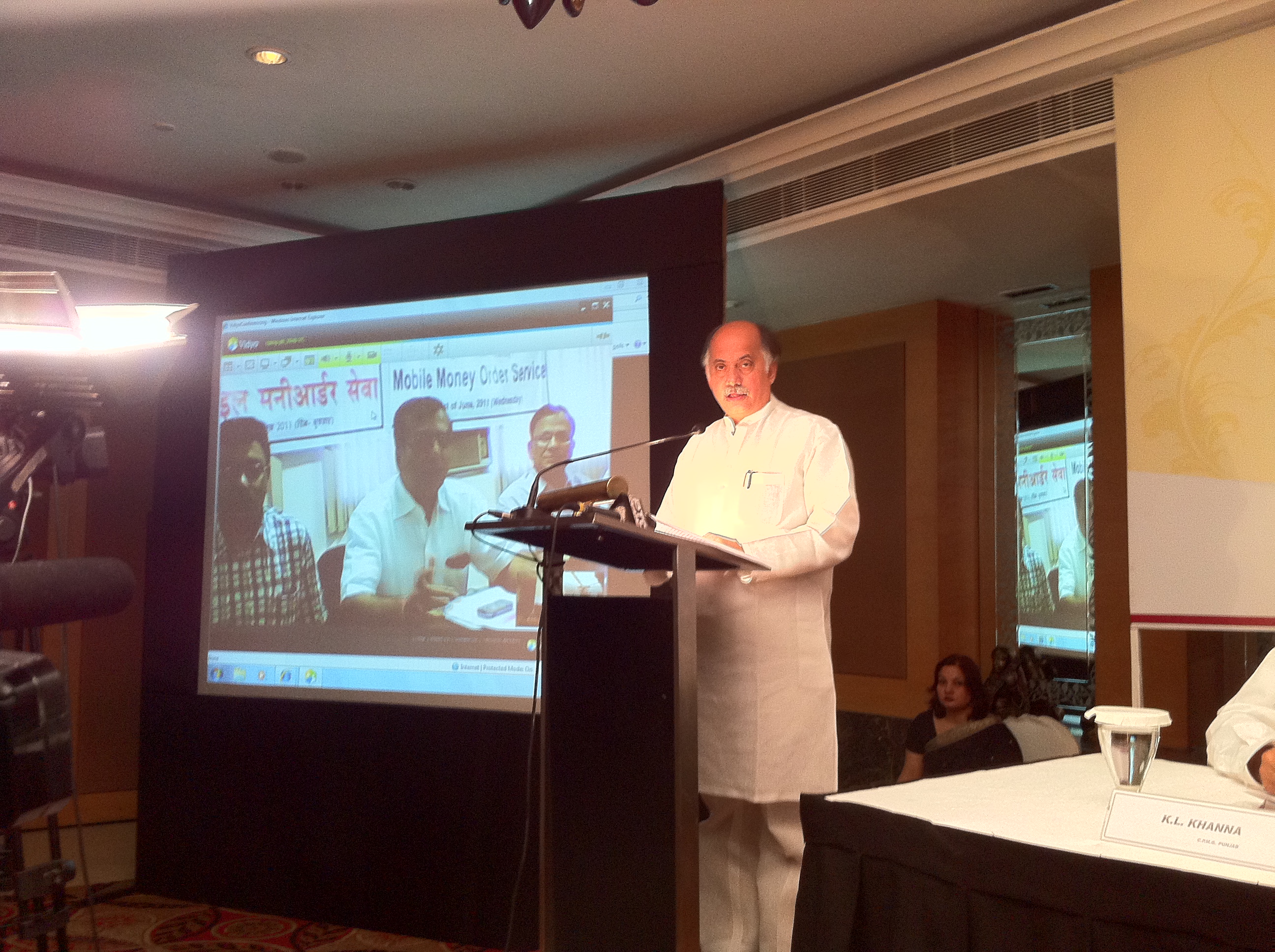





 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


