News
Haryana: Training cum Workshop On Harsamadhan Portal
Harsamadhan is the brand name of Centralized Public Grievance Redress and Monitoring System of Haryana. It was launched on 18th June 2010 at Haryana Niwas by Hon’ble Chief Minister of Haryana Sh. Bhupinder Singh Hooda. Harsamadhan portal is meant for citizens and departments of Haryana Government. ...
Inauguration of single window citizen facilitation centre at tahsil office premises, at Nabarangpur & Umerkote, Nabarangpur district, Odisha
Citizen Facilitation Centre has been inaugurated at Umerkote Tahsil on 21.04.2012 and at Nabarangpur Tahsil on 30.04.2012 by Sri Sibabrata Dash, IAS, Collector & District Magistrate, of Nabarangpur District with due assistance of NIC District Centre, Nabarangpur. Citizen/Beneficiary...
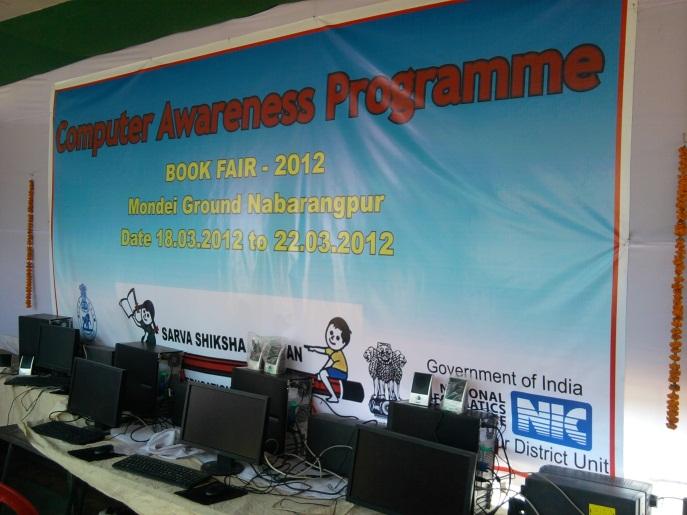
Free Computer Awareness Programme during BOOK FAIR 2012 Organized by District Administration & Sarva Sikhshya Abhiyan, Nabarangpur
A book fair was organized by District Administration & Sarva Sikhshya Abhiyan, Nabarangpur for 5 days at Nabarangpur District Headquarters. In the book fair one Free Computer Awareness Programme has been carried out by National Informatics Centre, District Unit, Nabarangpur for the children &...
Second prize to Chhattisgarh in National ePanchayat awards
Chhattisgarh has bagged the second prize in the national e Panchayat award for the implementation of the software PRIAsoft, Planplus and National Panchayat Portal in the state. The award was given by the Honarable Minister of Panchayati Raj Sh.V.Kishore Chandra Deo on 24th April 2012 on Panchayat...
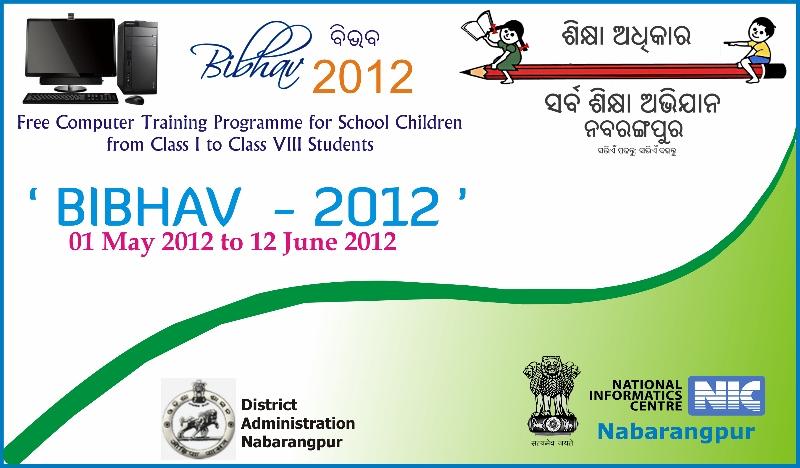
'BIBHAV - 2012' - A unique initiative to bridge Digital Divide at Nabarangpur, Odisha
45 DAYS FREE SUMMER TRAINING PROGRAMME ON COMPUTER FOR SCHOOL CHILDREN ORGANIZED BY DISTRICT ADMINISTRATION, SARVA SIKHSHYA ABHIYAN (SSA) AND NATIONAL INFORMATICS CENTRE (NIC), NABARANGPUR DISTRICT, ODISHA Being a tribal dominated district of undivided KBK region of Odisha the school children...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


