News
'BIBHAV - 2012' - A unique initiative to bridge Digital Divide at Nabarangpur, Odisha
45 DAYS FREE SUMMER TRAINING PROGRAMME ON COMPUTER FOR SCHOOL CHILDREN ORGANIZED BY DISTRICT ADMINISTRATION, SARVA SIKHSHYA ABHIYAN (SSA) AND NATIONAL INFORMATICS CENTRE (NIC), NABARANGPUR DISTRICT, ODISHA Being a tribal dominated district of undivided KBK region of Odisha the school children...
Launching of LFA (Local Fund Audit) Portal Odisha
- A G2G, G2E & G2C initiative of Finance Department, Govt of Odisha http : // lfaodisha.ori.nic.in Honourable Minister, Finance and Public Enterprises of Govt. of Odisha, Sj. Prafulla Chandra Ghadai inaugurated the launching of...
CMS Driven Meghalaya State Portal Launched
The performance report of the Government of Meghalaya was released on 3rd May 2012 at Shillong by the Hon’ble Chief Minister Dr Mukul Sangma. During this function the Chief Minister also launched the Meghalaya State Portal (meghalaya.gov.in or meghalaya.nic.in) and also the Meghalaya Online...
Centralized Public Procurement Portal Implemented in Andhra Pradesh
e- Procurement is a process which the physical tendering process is streamlined with ease of use and better efficiency without compromising the Government procedures. NIC has built a Centralized Public Procurement Portal for better transparency in procedures and saving in terms of time and money....
Inaugration of Virtual Class Room at National Institute of Technology, Jalandhar by Sh. Kapil Sibal, Hon ble Union Minister, MHRD
On 29.04.2012 Shri Kapil Sibal, Hon ble Union Minister, Human Resource Development, Communications and Information Technology, Govt. of India visited Dr. B. R. Ambedkar National Institute of Technology, Jalandhar and inaugurated Virtual Class Room Project over National Knowledge Network. He...




 Subscribe
Subscribe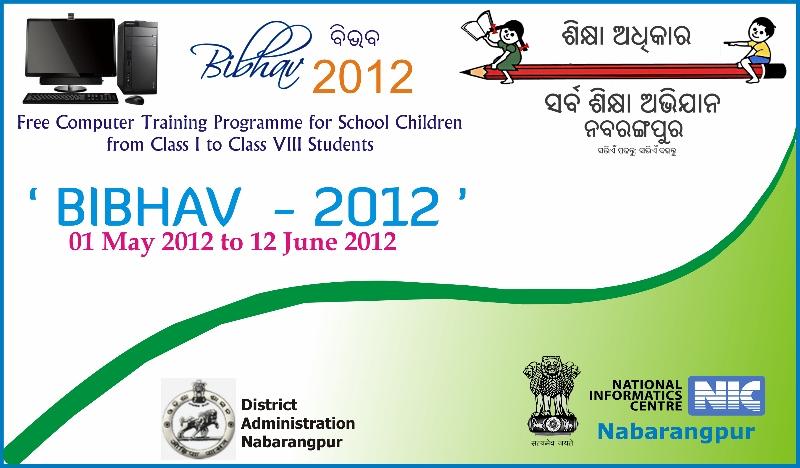





 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


