News
The World Classical Tamil Conference and Tamil Internet Conference 2010 (23.6.2010 to 27.6.2010)
The World Classical Tamil Conference was organized by the Tamil Nadu Government from 23rd June 2010 to 27th June 2010 at Coimbatore, Tamil Nadu. The conference was inaugurated by the Honorable President of India on 23rd June 2010. Tamil Internet Conference, which was organised as a part of the...
Workshop on Result Framework Document (RFD) for Senior Officers of Punjab at MGSIPA, Chandigarh
A two-day workshop on Result Framework Document (RFD) was organized by Punjab Government on 22-23 June, 2010 in Chandigarh. Hon’ble Finance Minister Punjab Sh Manpreet Singh Badal presided over the workshop. Dr. Prajapati Trivedi, Secreatary (Performance Management) Cabinet...
Launching of HarSamadhan (Centralized Public Grievance Redress and Monitoring System of Haryana)
Harsamadhan, a combination of two words Har (Everyone) and Samadhan (Solution), is an endeavor of the Haryana Government for fast Samadhan (Redress) of every kind of citizen’s grievances with a vision of pursuing excellence in e-Governance. Harsamadhan was launched on 18th June 2010 at Haryana...
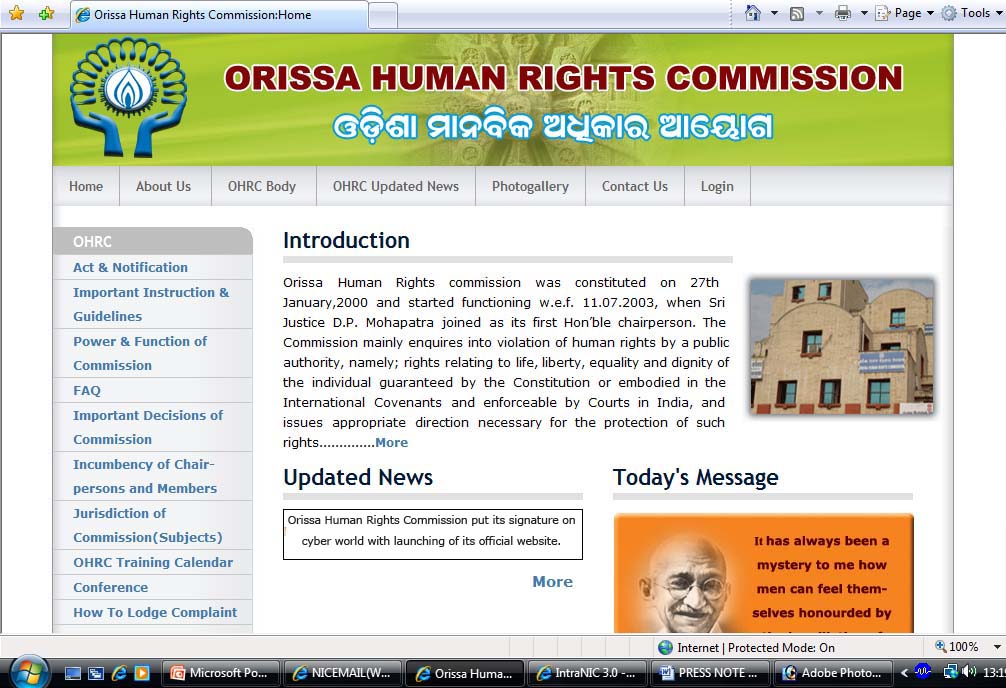
Orissa Human Rights Commission(OHRC) put its signature on cyber world
www.ohrc.ori.nic.in Orissa Human Rights Commission put its signature on cyber world with launching of its official website recently. Justice Radha Krishna Patra, Chairperson, OHRC inaugurated the website in presence of Dr. R.N. Bohidar, IAS, Member, OHRC, Shri Biswajit Mishra, IAS, Secretary,...
Bid opening of e-Tender of PMGSY::MANIPUR
Bid opening for PMGSY Manipur has been completed on 18/5/2010 in the presence of large number of enthusiastic officials and bidders. It took 2 days to open and show bid opening process including reading of scan files and showing in the projection screen for 562 bids for 69 packages. Altogether...

 Subscribe
Subscribe




 Flipbook
Flipbook PDF (6.8 MB)
PDF (6.8 MB)