Orissa Human Rights Commission(OHRC) put its signature on cyber world
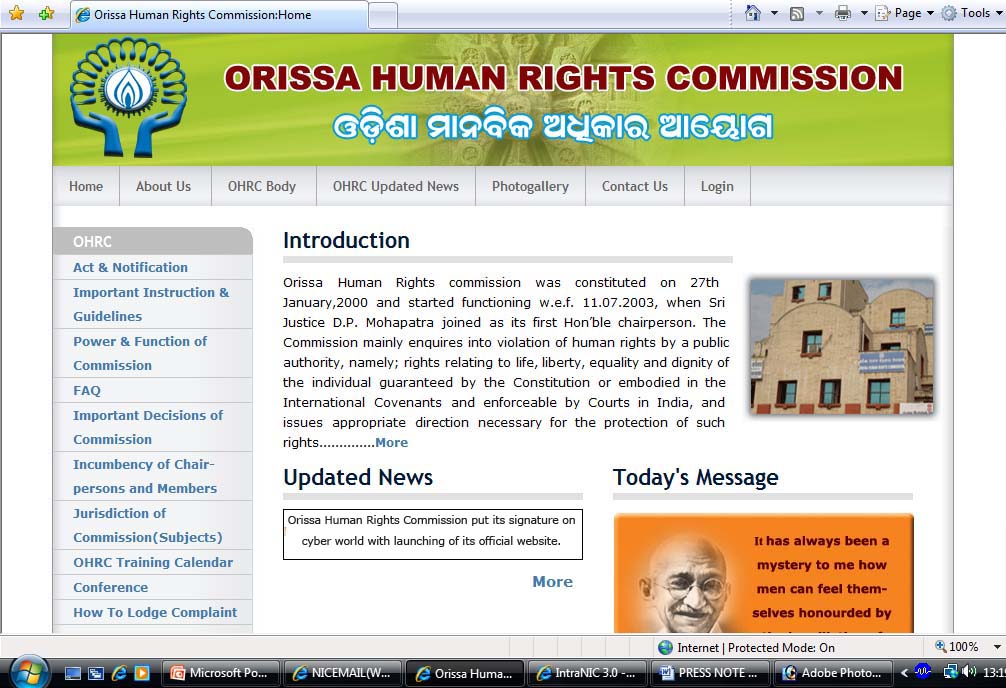
Orissa Human Rights Commission put its signature on cyber world with launching of its official website recently.
Justice Radha Krishna Patra, Chairperson, OHRC inaugurated the website in presence of Dr. R.N. Bohidar, IAS, Member, OHRC, Shri Biswajit Mishra, IAS, Secretary, OHRC, Shri A. K. Hota, Technical Director, Shri Ashis Kumar Mahapatra, Scientist-D, Shri Ram Prasad Mishra, NIC & other dignitaries.
This site will create awareness among common man about powers & functions of the Human Right Commission, Protection of Human Right Act-1993, relevant Notifications, guidelines on various rights issues, OHRC training / workshop calendar etc.
A complainant can be able to download the complaint registration form & able to know about how to file complaint with the OHRC.
Inaugurating the site, Chairperson appreciated the effort put in by NIC & informed that soon the online complaint system would be integrated with the website.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


