News
Honourable Chief Minister Orissa felicitates Shri S. K. Panda, SIO & Sr.T.D, NIC Orissa
On the eve of Local Self Governance Day, i.e. 31st August 2010, Hon’ble Chief Minister of Orissa Shri Naveen Patnaik felicitated Shri S. K. Panda, SIO & Sr.T.D, NIC Orissa State Unit at Jayadev Bhawan, Bhubaneswar, Orissa, for the contribution of NIC towards Urban Governance. Among...
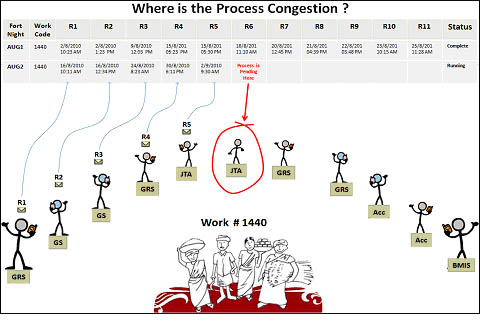
Addressing MGNREGA Issues Innovatively
District Ajmer in Rajasthan has leveraged SMS capabilities to know the work status of all MGNREGA works currently running in the district. District collector has achieved this with the association of CEO, Zila Parishad(ZP) , DIO NIC Ajmer and a Mumbai based software company Detha Infomedia Pvt. Ltd.SQRS...
State Level Training on MCH Tracking system organized at Panchkula, Haryana.
National Rural Health Mission, Haryana (NRHM), with technical support of NIC-Haryana organized a state level training for district officials in Panchkula during 23-28th August 2010. With conclusion of this training, Haryana becomes the first state for completion of State Level Training...
e-Sahooliat (Single Window System) launched at District Kathua, J&K
Hon’ble Minister for Revenue, Relief and Rehabilitation, Sh. Raman Bhalla and Minister of State for Information Technology, Dr. Manohar Lal Sharma inaugurated the e-Sahooliat (Single Window System) at Deputy Commissioner’s office Kathua on 28th August 2010 in the presence of MLA Kathua...
NIC Orgnanizes Regional Workshop on National Permits
NIC Punjab and Haryana jointly organized a regional workshop on National Permits Portal at CDAC Mohali. Ministry of Road Transport and Highways, Government of India sponsored the workshop. Officers from Transport Departments of Delhi, Punjab, Haryana, J& K, Chandigarh, Himachal Pradesh, Uttar...

 Subscribe
Subscribe




 Flipbook
Flipbook PDF (6.8 MB)
PDF (6.8 MB)