Agriculture
THE OILSEED DOCTOR & PULSE DOCTOR MAKE CHHATTISGARH FARMERS MIGHTIER
In a grand function held in Indira Gandhi Krishi Vishwavidyalaya (IGKV) Raipur, Chhattisgarh Android based Mobile Apps named Oilseed Doctor and Pulse Doctor were launched by Hon’ble Smt Krishna Raj, State Agriculture Minister, Govt. of India, on the 5th July 2018 in the presence of Shri Brij...
Indira Gandhi Krishi Vishwavidyalaya, Raipur, Chhattisgarh gets National eGovernance Silver Award for its Integrated Management Information System (IGMIS)
The project Integrated Management Information System (IGMIS) developed for Indira Gandhi Krishi Vishwavidyalaya (IGKV), Raipur by NIC Chhattisgarh State Centre, Raipur has been awarded with National eGovernance Silver Award during 20th National eGovernance Conference held on 9-10th Jan’2017...
Training Session on On-line Monitoring & Compliance Mechanism (DADF -eSamikSha) at Acharya Jagdish Chandra Bose hall, Krishi Bhawan,New Delhi on 14th June 2016
eSamikSha, an online Monitoring and Compliance Mechanism has been developed by Cabinet Secretariat Informatics Division, to fast track the compliance of pending action points, proposal, targets, etc. of Various Ministry/Department/Organization/Agency of Govt. of India and Government of States...
Honourable Chief Minister, Odisha, Shri. Naveen Patnaik inaugurated Seed DBT Automation System developed by NIC, Odisha State Centre
On the auspicious occasion of “Akshaya Tritiya”, a festival of farmers, Honourable Chief Minister of Odisha Shri Naveen Patnaik launched ‘Direct Benefit Transfer in Seed distribution’ for farmers of the state. The dignitaries present in the occasion include Honourable Minister...
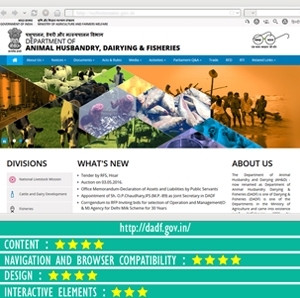
Department of Animal Husbandry Dairying and Fisheries
Department of Animal Husbandry Dairying & Fisheries (DADF) is one of the Departments in the Ministry of Agriculture. The Department is responsible for matters relating to livestock production, preservation, and protection from disease and improvement of stocks and dairy development, and also for...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


