Agriculture
JIND: Providing Innovative Technology Solutions for People
The district Jind derives its name from Jaintapuri, a town that grew around the temple of Jainti Devi (the goddess of victory) where Pandavas offered prayers for their success in their battle against Kauravas. It is one of the oldest districts of Haryana, comprising of 3 sub-dvisions, 4 tehsils,...
MALKANGIRI: e-Governance in the land of Primitive Tribes
Malkangiri district came into existence after the reorganization of Odisha state on 2nd October 1992. Covering an area of 5,791 sq. kms, almost the whole of district is covered with vast dense jungles, with tribal population comprising of primitive tribes notable among them are Bondas, Koyas,...
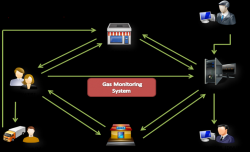
EASYGAS, KISAN: Citizen-Centric IT Innovations from Gonda, Uttar Pradesh
Achieving milestone is not an everyday business. Claiming appreciation for achievement is even tougher. The feeling goes beyond the expected elation, when endeavour, designed and perspired for common good catches peoples eyes to attain recognition. Project EASYGAS and project KISAN, the two...
eDMAIs-Delivering Mechanized Agricultural Implements System
Improved farm implements and machinery are used for different farm operations to increase productivity of land and labour through timeliness of operations, efficient use of inputs, improvement in the quality of produce, safety and comfort of farmers, reduction in loss of produce and drudgery...
ROHTAS: Empowering the Masses through e-Governance
Sasaram, the administrative headquarters of the district Rohtas (Bihar) - a place of historical importance, is surrounded by Bhojpur and Buxar district in the North, by Palamu and Garwah in the South, Aurangabad and a part of Gaya in the East and by Kaimur district in the West. Famous for the Tomb...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


