Health
Hon'ble Governor and Hon'ble Chief Minister HP Launch Ayushman Bharat in All Districts Using NIC VC
The Ayushman Bharat scheme was launched in all Districts of Himachal Pradesh by Hon’ble Governor, Acharya Devrat and Hon’ble Chief Minister, Sh. Jai Ram Thakur using NIC Video Conferencing set up, on 23-Sep-2018 from Shimla. The live webcast of the event from Ranchi was also viewed in...
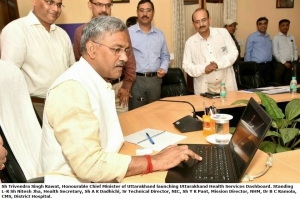
Launch of Uttarakhand Health Services Dashboard by Chief Minister
Sri Trivendra Singh Rawat, Honourable Chief Minister of Uttarakhand has launched Uttarakhand Health Services Dashboard developed by NIC Uttarakhand. It is convergence of vital information at a single platform of all those parameters which are significant for maintaining quality...
J and K : Principal Secretary to Government, Health & Medical Education, J&K launched XLN- Extended Licensing Node
SRINAGAR, Aug 13: Principal Secretary Health & Medical Education, Dr Pawan Kotwal launched online licensing system for obtaining drug license and its renewal of retail sale and wholesale establishments. Drugs & Food Control Organization (D&FCO) J&K in cooperation with NIC’s XLN...
Honorable Minister Health and Medical Education J&K Government reviewed e-Hospital@NIC
Hon’ble Minister for Health and Medical Education, J&K Government, Dr. Devinder Kumar Manyal chaired maiden meeting of Health Department and also reviewed the functioning of e-Hospital@NIC project running at Govt Hospital Gandhi Nagar Jammu as well as at 02 District Hospitals, 04 sub-district...
Haryana:- Sharing of Best Practices - MedLEaPR and FSL#MedLEaPR in National Level Training of Trainers at CDTS, Chandigarh
Training of Trainers Programme for Judicial, Prison, Prosecution and Police officers was held between 9-10 October 2017 at the Central Detective Training School, Chandigarh. Mr. Rahul Jain, Technical Director, NIC-Haryana was invited as resource...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


