Transport
Online Rohtang Pass Permits Issuance System
To make it easier for the Rohtang Pass commuters, the payment gateway has been integrated with the system so that all the charges can be paid online and the permit is issued on successful receipt of payment by the Department. This web application is a unique mode of getting permits.
MUZAFFARNAGAR: Treading fast on e-Governance turf
Muzaffarnagar, located in the northern part of Uttar Pradesh is popularly known as The Sugar Bowl of India. With a population of 41,38,605 (Provisional figures of the 2011 census of undivided Muzaffarnagar) the district spreads over an area of 4049 square kilometers and has 4 tehsils, 9 development...
Manipur-Providing e-Services at District Transport Offices
Vahan and Sarathi are standardised software applications developed by NIC Hq. to meet the twin objectives of Ministry of Road Transport and Highways (MoRTH) towards adopting standard data formats and software for vehicle registration and driving licences so as to build a national register of vehicles...
NATIONAL TRANSPORT REGISTER
Over the past decade or so there has been an island of e-Governance initiatives by state transport authority of different States in the country. The experience with the IT initiatives, have been very good and is extremely beneficial in making transport department services accessible to the common man...
Zunheboto : Providing ICT based Services & Support in Nagaland
Among the six districts of the Nagaland state, Zunheboto is situated in the middle bounded by Mokokchung in the East and Wokha district in the West. Tizu, Doyang and Tsutha - the three important rivers of the district are source for hydel power generation and terrace cultivation.High hills...




 Subscribe
Subscribe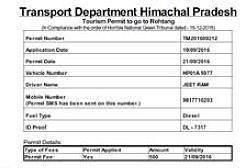





 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


