ICT in Districts
Mainpuri District, Uttar Pradesh The haven for migratory birds showcases its marvelous use of ICT for e-Governance
Since its inception in 1989, National Informatics Centre (NIC), Mainpuri has played a pivotal role in implementation of various ICT Projects in the district. NIC is playing key role in extending technical expertise to District Administration in ICT initiatives and implementation of...
Faridkot District, Punjab Transforming the Rural District into Advance Digital One
Since its inception in late 80, the District Unit is a pioneer in designing, developing and implementing many e-Governance Projects with an objective to use electronic means to support and stimulate good governance. NIC Faridkot is instrumental in rolling out the ICT awareness in the...
Hisar District - Signature of excellence in Innovative ICT at grass-root Informatics
NIC District Centre, Hisar has been extending its ICT enabled support and services to the District Administration and various departments of the State Government and Central Governments by commissioning State-of-the-art infrastructural including three Video Conferencing studios, IT...
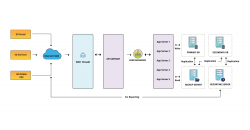
Integrated ShalaDarpan - Decision Support System for Schools Monitoring & Management
ShalaDarpan is a unique idea to provide an end-to-end solution to the Education department for effective monitoring and management of all Government Schools. System facilitates decision support, Planning (School Open/ Upgrade/ Merge/ Close), School operations (Admissions, Promotions,...
Akola District - Pioneer with excellence in digital governance at the Cotton City of India
NIC, Akola is a pioneer with excellence in digital governance, with communication facilitation, technical support, system analysis, and innovative implementation of ICT. NIC, Akola is recognized with more than twenty various types of awards and recognitions for innovative initiatives...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


