Technology
Emerging AI/ML Attacks and Risk Navigating Emerging AI/ML Threats in Application Security
In the era of relentless innovation driven by Artificial Intelligence (AI) and Machine Learning (ML), applications are gaining remarkable capabilities. From intelligent chatbots to precise data analysis, these technologies hold immense promise. However, they also bring vulnerabilities that malicious...
ePrayuktiSewa Online Portal for Mobile App & Bharat Map Service
e-PrayuktiSewa, created by NIC Assam, is a platform that helps government entities in Assam make better decisions, allocate resources wisely, and stay aware of their surroundings. It does this by offering tools like the Mobile App Builder, Bharat Map services, and AI algorithms, which allow government...
SugamyaWeb Enabling accessible web experience of the Indian Governments websites
SugamyaWeb is a cloud enabled Web Accessibility reporting platform, which provides end-to-end web testing. The tool classifies and prioritizes accessibility issues based on end user impact along with recommendations on how to fix the issue. So, as to enable the teams to target the right to fix, instead...
Puducherry UT French Riviera of the East
NIC, Puducherry UT plays a vital role in designing, developing and implementing ICT solutions which has helped in achieving transparency and efficiency in the delivery of the citizen centric services. In addition to core infrastructure for networks, VC and cloud services, NIC Puducherry has established...
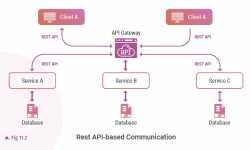
REST vs. Messaging for Microservices Discover how to choose the right communication style for Microservices
Two common protocols used in microservices are HTTP request/response with resource APIs and lightweight asynchronous messaging when communicating updates across several microservices. This way the small, lightweight modules in MSA architecture can achieve the business domain process. MSA is the established...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


