Technology
GePNIC Presentation at Hindustan Shipyards Ltd., Visakhapatnam
Hindustan Shipyard Ltd. (HSL), Visakhapatnam, a fully owned Government of India undertaking under the Ministry of Defence, has shown its interest to implement GePNIC- the NIC e-Procurement System. HSL is nation’s premier shipbuilding organisation catering to the needs of shipbuilding,...
NIC Initiatives Impress US Prez
NIC Initiatives Impress US President GPNIC has been developed to facilitate the Panchayat offices by providing various online services. Ten gram panchayats of Srinagar block (Ajmer) ,Rajasthan were selected on a pilot basis .BSNL had provided optical fiber based...
NIC Orissa State Centre Bhubaneswar shares Liquid Love
There is no gift, more precious than life. And Blood, runs through the very veins of this gift. Also there is no substitute of this gift, the lifeline of human existence. NIC Orissa State Unit in association with the Indian Red Cross Society, organized the voluntary Blood Donation Camp in memory of...
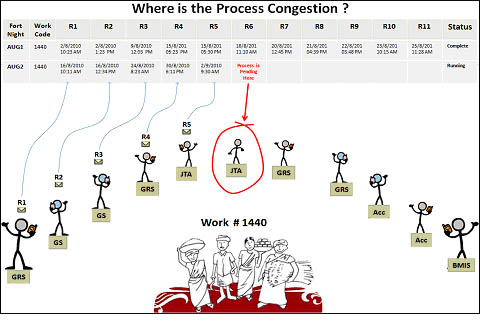
Addressing MGNREGA Issues Innovatively
District Ajmer in Rajasthan has leveraged SMS capabilities to know the work status of all MGNREGA works currently running in the district. District collector has achieved this with the association of CEO, Zila Parishad(ZP) , DIO NIC Ajmer and a Mumbai based software company Detha Infomedia Pvt. Ltd.SQRS...
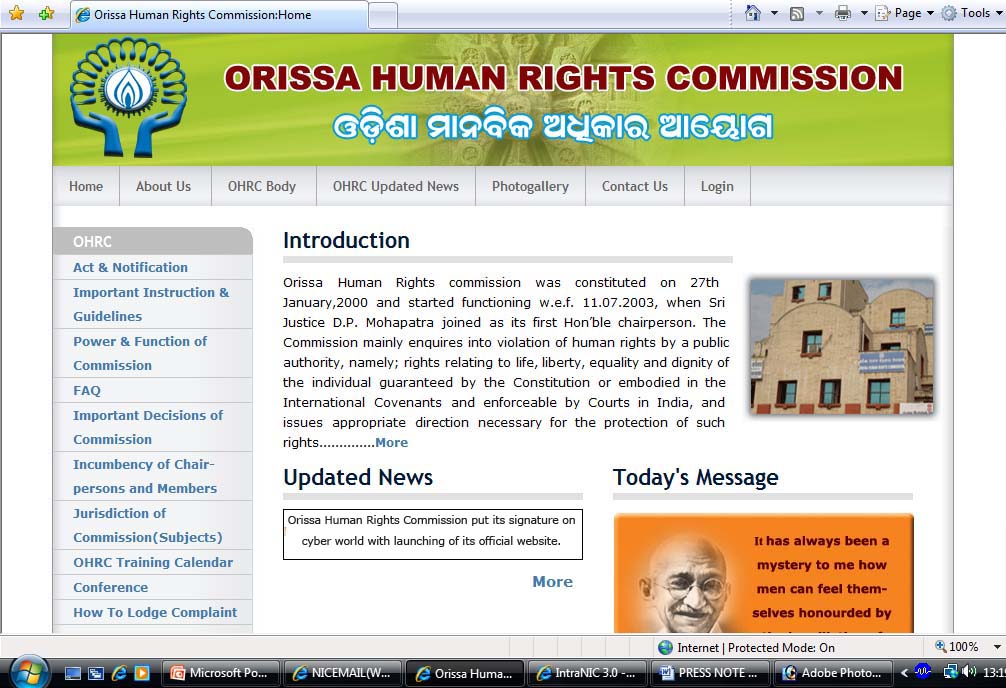
Orissa Human Rights Commission(OHRC) put its signature on cyber world
www.ohrc.ori.nic.in Orissa Human Rights Commission put its signature on cyber world with launching of its official website recently. Justice Radha Krishna Patra, Chairperson, OHRC inaugurated the website in presence of Dr. R.N. Bohidar, IAS, Member, OHRC, Shri Biswajit Mishra, IAS, Secretary,...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


