Standardization
REST vs. Messaging for Microservices Discover how to choose the right communication style for Microservices
Two common protocols used in microservices are HTTP request/response with resource APIs and lightweight asynchronous messaging when communicating updates across several microservices. This way the small, lightweight modules in MSA architecture can achieve the business domain process. MSA is the established...
eGramSwaraj Simplified Work-based Accounting application for Panchayati Raj
eGramSwaraj has improved the functioning of Panchayati Raj Institutions, providing citizens with a platform to connect with local representatives and participate in local governance. It has enabled greater transparency and accountability in the functioning of the Panchayats, which has been essential...
PM CARES for Children Portal Ensuring Successful Implementation of PM CARES for Children Scheme
PM CARES for Children portal was envisaged as a one-stop-solution for bringing all the aspects of child welfare covered under PM CARES for Children scheme at one place viz. financial assistance, boarding & lodging, healthcare, scholarship & educational support. The platform was designed to...
Government Email Service Enabling secure communication channel within the Government
The importance of Email Service was evident during the ongoing pandemic as it ensured that communication within the Government is not impacted by COVID-19 and continues to operate seamlessly. The service is the largest service of its kind ffered by any Government globally.
Gujarat CM Dashboard - Enabling government machinery for strengthening good governance
The system first of its kind was an innovation in terms of accessing data from all e-Governance applications of the State of Gujarat and providing the same for monitoring against defined KPIs. In the reverse, CMO could drill down to the granular level on the fly for red-flagged items and intervene...




 Subscribe
Subscribe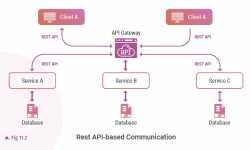





 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


