Standardization
Infrastructure Setup for Software Testing
The 'Test Bed Setup', an initiative of Software Development Unit (SDU) at NIC HQ, New Delhi, comprise of six high end servers in Linux and Windows environment. These servers can be used as staging environment temporarily, for deployment of applications under testing apart from generating virtual...
Standardization of District Portal with Web CMS
One of the recent challenges a country faces is preparing its citizens and government for globalization and information and communication revolution. Information and Communication Technology (ICT) plays a pivotal role for instituting effective e-Governance, which essentially bridges the gap between...
Mobile enabled citizen services through 2D Barcodes
Barcode is used to encode Edited by R.Gayatri data for variety of purposes. 2D barcode can be used in e-governance applications to benefit the Government and the citizen at large.The 2D barcode is readable using mobile camera, web camera and scanners alike. As the mobiles have the GPRS/3G connectivity...
Leveraging Web 2.0 in Government
A new genre of Web-based applications has gained a lot of popularity in last few years. Applications such as Facebook, YouTube, MySpace, Twitter, once a tool of tech savvy youngsters have gained a lot of popularity and acceptance across much wider spread of demography. Social-networking Web sites,...
Guidelines for Indian Government Websites
Web enablement of citizen services is one of the focus areas of NeGP (National e-Governance Plan). Communication and literacy expression are the key indicators of a successful relationship and websites are the first point of interface in building these relationships. They also facilitate an efficient...




 Subscribe
Subscribe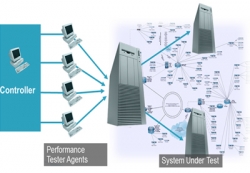




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


