ICT Initiatives
National eGov App Store: Reusable Application Availability Store
Application stores are ideal solutions for hosting applications and components that can be re-used by other departments at the Centre and the States without investing cost and efforts in development of the same. As a precursor for realizing the importance of application stores, NIC developed...
Rollout of e-Panchayat MMP in Bihar
To make Panchayats accountable, transparent, inclusive and empowered, e-Panchayat Mission Mode Project under National e-Governance Plan is being rolled out at all the three tiers of Panchayati Raj Institutions (PRIs), viz. 38 District Panchayats, 531 Block Panchayats and 8398 Gram Panchayats...
KULLU: Leveraging ICT in Dev Bhoomi
Kullu, known as the Valley of Gods and Apples, derives its name from the word KALUT which was a tribe in the upper valley of River Beas. It is famous for International Folk Dance festival and Kullu Dussehra. The district comprises of 4 Sub-Divisions, 7 Tehsils, 2 Municipal Corporations, 3...
MyGov Platform: Heralding a New Era in Governance
National Informatics Centre, DeitY was entrusted with the task of coming up with an online platform, which bridges the gap between people and government through effective citizens participation in the process of governance. Being the frontrunner in facilitating many innovative e-Governance initiatives of...
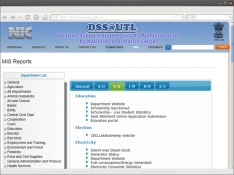
NIC-eDSS: Decision Support System of Lakshadweep Administration
Decision Support Systems (DSS) are interactive, computerbased systems that aid users in judgment and choice activities. They provide data storage and retrieval along with enhancing the traditional information access and retrieval functions with support for model building and model-based reasoning. They...




 Subscribe
Subscribe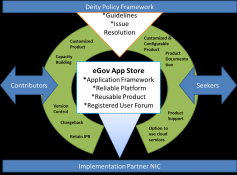




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


