ICT Initiatives
POWERING GIGW COMPLIANCE
In the last decade or so, India has metaphorically witnessed a lot of water surge & not just meekly flow under the bridge. Technology has played an increasingly prominent role as enabler and leveller. Enabler- Technology continues to bring a flood of opportunities to lead lives very differently...
COMBATING MALNUTRITION & UNDER-5 MORTALITY IN NAGAON DISTRICT OF ASSAM THROUGH ICT
Launched on October 2, 1975, the Integrated Child Development Service (ICDS) Scheme today represents one of the worlds largest and most unique programmes for early childhood development. In the case of Nagaon District, the mortality rate of children below 5 years has been higher than the average...
GoI Search as a Service (GoI-SaS)
Government of India (GoI) Search Platform initiative has enabled the citizens and other stakeholders to quickly access the data on Government websites. Under this initiative, Search as a service (GoI-SaS) facilitates the website owners in the Government to define their own search interface...
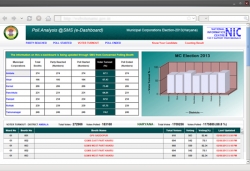
ICT in Local Bodies Elections in Haryana
The local bodies elections conducted by State Election Commission (SEC), evoke huge enthusiasm and interest amongst the public and political parties. Usually the number of candidates taking part in such elections is very large. Due to high percentage of votes polled, the value attached to each...
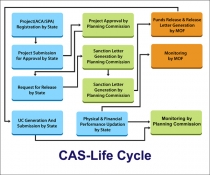
CAS : MIS on Central Assistance to the States
With altering paradigms of Information and Communication Technology, NIC Cell at Planning Commission is on a constant endeavour to cater to the diverse requirements of various divisions of the Planning Commission of India. The e-Governance movement in country today has witnessed a complete facelift...




 Subscribe
Subscribe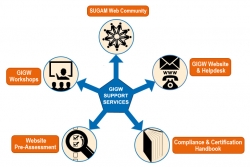



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


