ICT Initiatives
Haryana:- DIO Sirsa commended by State Minister of Labour & Employment during International Geeta Jayanti Mahotsav 2017 at Sirsa
International Geeta Jayanti Mahotsav 2017 was celebrated in Ch. Devi Lal University, Sirsa (Haryana) w.e.f. 28.11.2017 to 30.11.2017. Sh. Naib Singh Saini, State Minister of Labour & Employment Haryana, Dr. Vijay Kumar Kayat, Vice Chancellor CDLU and Dr. Munish Nagpal, Addl. Deputy Commissioner...
Training on Singrauli-eSamikSha (an Online Monitoring and Compliance Mechanism) via Video Conferencing held on 21st November 2017.
eSamikSha, an online Monitoring and Compliance Mechanism has been developed by Cabinet Secretariat Informatics Division, to fast track the compliance of pending action points, proposal, targets, etc. of various Ministry/Department/Organization/Agency of Govt. of India and Government of States and...
Hon CM of Maharashtra inaugurated the Website and GIS Portal of Slum Rehabiliation Authority of Maharashtra on 21 November2017
The website (http://sra.gov.in) and GIS Portal of Slum Rehabilitation Authority of Maharashtra (http://umd.nic.in/sra) developed with the technical support of NIC was inaugurated on 21 November 2017 at CM Secretariat Mumbai by Hon. Chief Minister of Maharashtra in the presence of State Housing Minister,...
Grass-root Level Workshop-cum-Training on AEBAS at Mahanadi Coalfields Ltd. (MCL), Sambalpur, Odisha
“Digital India” programme of Government of India seeks to transform India into a digitally empowered society and knowledge economy. As part of this programme, Deity / NIC / UIDAI have implemented Aadhaar Enabled Biometric Attendance System (AEBAS) in all Central Government offices....
F.L Dealers Meet on e-Payment Module for the Retailers of Chandikhol Depot for Online Process of Odisha State Beverages Corporation Limited (OSBCL)
One day training cum workshop was organised by State Bank of India on 22nd June’ 2017 at Jajpur Road for the retailers of Chandikhol Depot of Odisha State Beverages Corporation Limited (OSBCL), Bhubaneswar, Odisha. Officers of National Informatics Centre (NIC), Bhubaneswar, Odisha State Beverages...




 Subscribe
Subscribe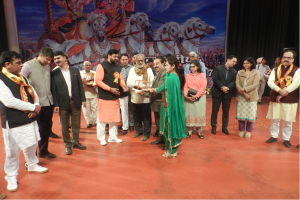




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


