Biometric Authentication
IDENTITY CARD MANAGEMENT SYSTEM (ICMS)
Identity Card Management System (ICMS) is a fully integrated system that identifies individuals of an organization by way of issuing Identity Cards (ID Cards). It assists in controlling access to the resources of an organization on the basis of such ID Cards. The new system provides...
MedLEaPRFIRST STEP TOWARDS ICT ENABLED INTEGRATED JUSTICE DELIVERY SYSTEM
Medico Legal Examination and Postmortem Reports System (MedLEaPR) is a generic software developed by NICHaryana to facilitate computerization of MLRs & PMRs. Further, the system is workflow based, which provides requisite access security, based on roles & responsibilities...
Biometric Authentication: IRIS image Capture, Storage and Processing
In this era of Information technology, we all have multiple accounts and use multiple passwords on host of computers and Web sites for checking e-Mail, managing bank accounts, online transactions etc. Maintaining and managing access while protecting both the user's identity and the computer's...
"Krushak Samrudhi"- A Unique ICT Initiative to Empower Farmers
Exclusive talk with Sh. Ashok K.K. Meena, IAS Commissionercum- Secretary, Food Supplies and Consumer Welfare Department, Govt. of Orissa.
Dholpur: ICT Shines on the Eastern Gateway of Rajasthan
Situated in the eastern part of Rajasthan bordering Uttar Pradesh and Madhya Pradesh, Dholpur earlier called Dhavalpur, was carved out of Bharatpur in 1982. It is famous for its sandstone and ravines which are part of Chambal legacy. The famous Dholpur House (UPSC HQ), President House and...




 Subscribe
Subscribe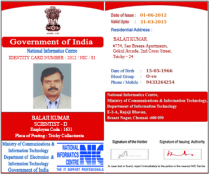





 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


