Digitization
International Co-operation: India's ICT Team Visits Sri Lanka
Hon'ble Prime Minister of India, Shri Narendra Modi at 18th SAARC, has envisioned making the region more connected and prosperous. His vision for the region rests on the primary pillars of trade, investment, assistance, cooperation, people-to-people contacts and seamless connectivity.
VISAKHAPATNAM, Andhra Pradesh
NIC District Centre, Visakhapatnam, since its inception has been instrumental in developing and successfully implementing various ICT based initiatives in the District besides its role in spreading the ICT culture among the Government Departments. The success stories are many and the efforts...
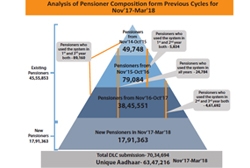
JEEVAN PRAMAAN Digital Life Certificate
Since its implemention in 2014, over 1.6 crore DLCs have been submitted by over 90 lakh pensioners. 3.01 lakh DLCs were submitted in a single day on 13th Nov, 2017. Peak utilization of the system was observed as 1,205 DLCs per minute on 9 Nov, 2017 at 11:36 AM. Jeevan Pramaan ecosystem has...
e-HRM System for Government by NIC
This recently launched Application enables creation of e-Service book of employees from physical service book and automate the updation of e-Service book. This makes day-to-day processing of various records of employee possible, resulting in real time updation of servicebook and uniform implementation...
Online GPF System of Arunachal
Catering to the need of Directorate of Accounts and Treasuries by incorporating all the features required for maintaining GPF accounts and generating all essential reports and statements, the online GPF System follows a very transparent approach in providing a comprehensive resource of information...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


