G2C
e-Archives: Online Cataloguing System for Odisha State Archives, Bhubaneswar
e-Archives is an online cataloguing system developed by NIC for Odisha State Archives(OSA) to facilitate systematic collection (scanning and storing), preservation, management, publication and educational use of the rare records and historic documents digitally. One of its kinds, the e-Archives software...
e-Services for Council of Higher Secondary Education - A successful approach in Manipur
NIC Manipur has been providing ICT services to the Council of Higher Secondary Education, Manipur (COHSEM) since the year 2003. In the year 2004, the Application software for omputerization of the entire process of examinations conducted under this council was developed and the results of these examinations...
Digital India Week (Launch on 01st July, 2015 at Indira Gandhi Indoor Stadium, New Delhi)
Digital India, a flagship programme of the Government of India, aims to transform India into a digitally empowered society and knowledge economy. This programme centres on three key vision areas of Infrastructure as a Utility to Every Citizen, Governance and Services on Demand and Digital Empowerment...
e-Shramik: Online Registration for Welfare of Odisha Building and Other Construction Workers
The Odisha Building and Other Construction Workers Welfare Board (OB&OCWW) was constituted to regulate the employment and service condition of building and other construction workers and to provide them safety, health and welfare measures. e-Shramik project aims to facilitate the construction workers...
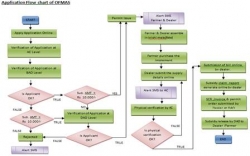
OFMAS: Online Farm Mechanization Application Software of Bihar
Bihar, with the help of modern technology, scientific methods and high quality inputs can easily double the agricultural production and enrich the quality of life in rural areas. However, the major challenge is the inadequacy of farm power and machinery with the farmers for increasing agricultural productivity....




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


