Articles
Implementation of IVFRT MMP in Odisha
This is an exclusive interview with Shri Lalit Das, IPS & Special Secretary, Home Department, Govt. of Odisha on various paradigms along with challenges faced during implementation of Immigration Visa and Foreigners Registration (IVFRT) Mission Mode Project in Odisha.
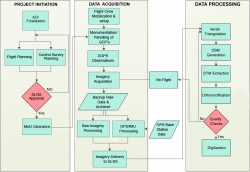
Use of Hybrid Survey Methodology and Bhu-Sarvekshan Software for Resurvey in Bihar
The Bihar state - spread over approx. 94163 sq. Km area, has an administrative setup comprising of 9 divisions, 38 districts, 101 subdivisions, 534 circles and 45,700 mauza(s) i.e. revenue villages. The very first survey of land i.e. Cadastral Survey (CS) of the state was conducted almost a century ago....
Goa Excise Management System (GEMS)
GEMS is Government to Business (G2B) initiative of Department of Excise, Government of Goa, aimed at achieving good governance and paperless office using ICT tools. The project was entrusted with NIC in October 2013, to develop a complete web based workflow application providing end-to-end solution...
Unified Birth and Death Registration System in Andhra Pradesh
ITE&C Department, Govt. Andhra Pradesh has initiated Civil Registration System- Unified Births & Deaths Registration, a Flagship project, for computerization of Civil Registrations for RLBs (Rural Local Bodies) and ULBs (Urban Local Bodies) in consultation with Commissioner & Director...
KhoyaPaya: Citizen Centric Portal Missing and Vulnerable Children
Children are the most vulnerable section of our society and are observed as the easy and soft target of criminals and perverts. The worst among the atrocities encountered by children are trafficking, kidnapping and sexual abuse. Despite the law enforcement agencies does their best to safeguard...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


