Articles
Online GIS Monitoring System
The online GIS monitoring system for sericulture development in Manipur is a solution for monitoring the progress of sericulture plantation using GIS, Satellite Imageries, Geo-tagged photographs and Vegetation Data.
Good Governance Week Celebration 2015
One of the key enablers of a country growth and prosperity is good governance. Progressive yet focussed efforts of a government to strive for excellence in administration, efficiency in providing public services with the optimal utilization of public money and inclusive participation of citizens in government...
District Una: Ahead in e-Governance
Located in the southwestern region of the beautiful State of Himachal Pradesh, the district of Una geographically spreads across an area of 1,540 sq. kms. Una was formed on the 1st of September 1972 with the district headquarter situated 240 Kms from the Himachals capital Shimla. Una is 120 Kms away...
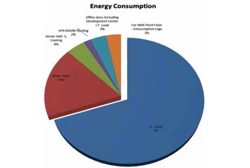
NDC Shastri Park, Delhi: Power Usage Effectiveness (PUE) achievement
In order to meet the ever increasing need of high availability and reliability of mission critical applications of the government, National Informatics Centre (NIC) has set up its world class National Data Centre (NDCSP) at Delhi IT Park (Shastri Park, Delhi). The NDC has been designed to provide full...
Village level online e-Services in Goa: Taking Governance to the grassroots
The beautiful State of Goa is geographically small compared to many other Indian States. The long Konkan terrain spreading across its many regions and the limited availability of public transportation system makes the travel especially for those from the farflung villages quite difficult. Citizens had...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


