Articles
API Management Solution at MyGov: Publish, manage, secure and analyze APIs in minutes
The API Management Solution deployed at MyGov facilitates the connection of data and business functions. MyGov uses Tyk as its API Gateway and API Dashboard.
Jal Shakti Application: Enabling seamless monitoring of countrywide campaign through Portal and Mobile App
In a countrywide effort to enhance water security, especially in water-stressed districts, the Centre initiated Jal Shakti Abhiyan (JSA) in all states of the country. JSA Portal and JSA Android Mobile App are designed with an aim to track several activities and tasks related to the campaign at...
Simultaneous Parliamentary and Assembly Elections 2019 in District Tirap: Smooth management through effective intervention of ICT-enabled applications
The development of IT applications for election management has automated the work of the Election Commission of India (ECI), thereby speeding up operations and enhancing efficiency. NIC Tirap has helped District Authorities utilize the applications developed by ECI to conduct elections at...
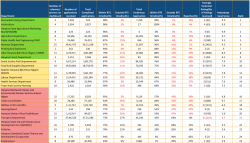
Antyodaya SARAL Haryana: A unified platform ensuring hassle-free & time-bound delivery and tracking of G2C services in the State
Having implemented Antyodaya SARAL, Haryana is the first state in the country to integrate so many schemes and services on one platform. The powerful solution developed by NIC Haryana has channelized the process of bringing about a fundamental behavioral change in the way the government functions, and...
South Tripura District: Rising up to challenges and leaving impact through futuristic e-Governance solutions
Since its inception in September 2014, NIC South Tripura has been playing a pivotal role in facilitating an efficient e-Governance infrastructure and providing ICT-enabled services to the citizenry. The implementation of digitally empowered services such as eDistrict, Vahan & Sarathi, Land Records/...




 Subscribe
Subscribe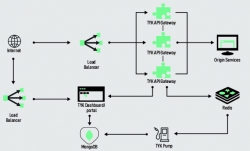




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


