News
Haryana Wakf Board goes on-line
On Monday, the February 7, 2011, Shri Vivek Mehrotra, IAS, Secretary, Ministry of Minority Affairs, Govt. of India (MoMA) inaugurated the Centralized Computing Facility (CCF) established at Haryana Wakf Board, Ambala (HWB) under the Project “Computerization of Records of the State Waqf Boardsâ€...
GIGW Workshop
Orientation Cum Training Programme on GIGW Held A two day comprehensive workshop of NIC officials on GIGW (Guidelines for Indian Government websites) was held on the 19-20th Jan. 2011 at Secretariat Jaipur. More than seventy NIC officer's from the district and the state unit...
Chief Minister, J&K Launched e-Tendering portal for PMGSY
Hon’ble Chief Minister, Jenab Omar Abdullah formerly launched e-tendering Portal http://pmgsytendersjk.gov.in for PMGSY under Public Works Department, on 3rd February, 2011, in a very simple and impressive function organized at Civil Secretariat Jammu. Among others following were...
Cadastral Maps (Mussavies) Digitization & Integration of Bhu-Naksha & HALRIS
One Cadastral Maps digitization Lab & Integrated Bhu-Naksha & HALRIS software solutions has been set up for 40 on-line villages of Ambala Tehsil at Mini Secretariat Ambala. On 20th January, 2011, FCR Sh. Naresh Gulati has reviewed and inspected the lab. The complete demonstration of HARIS-HALRIS-Bhu...
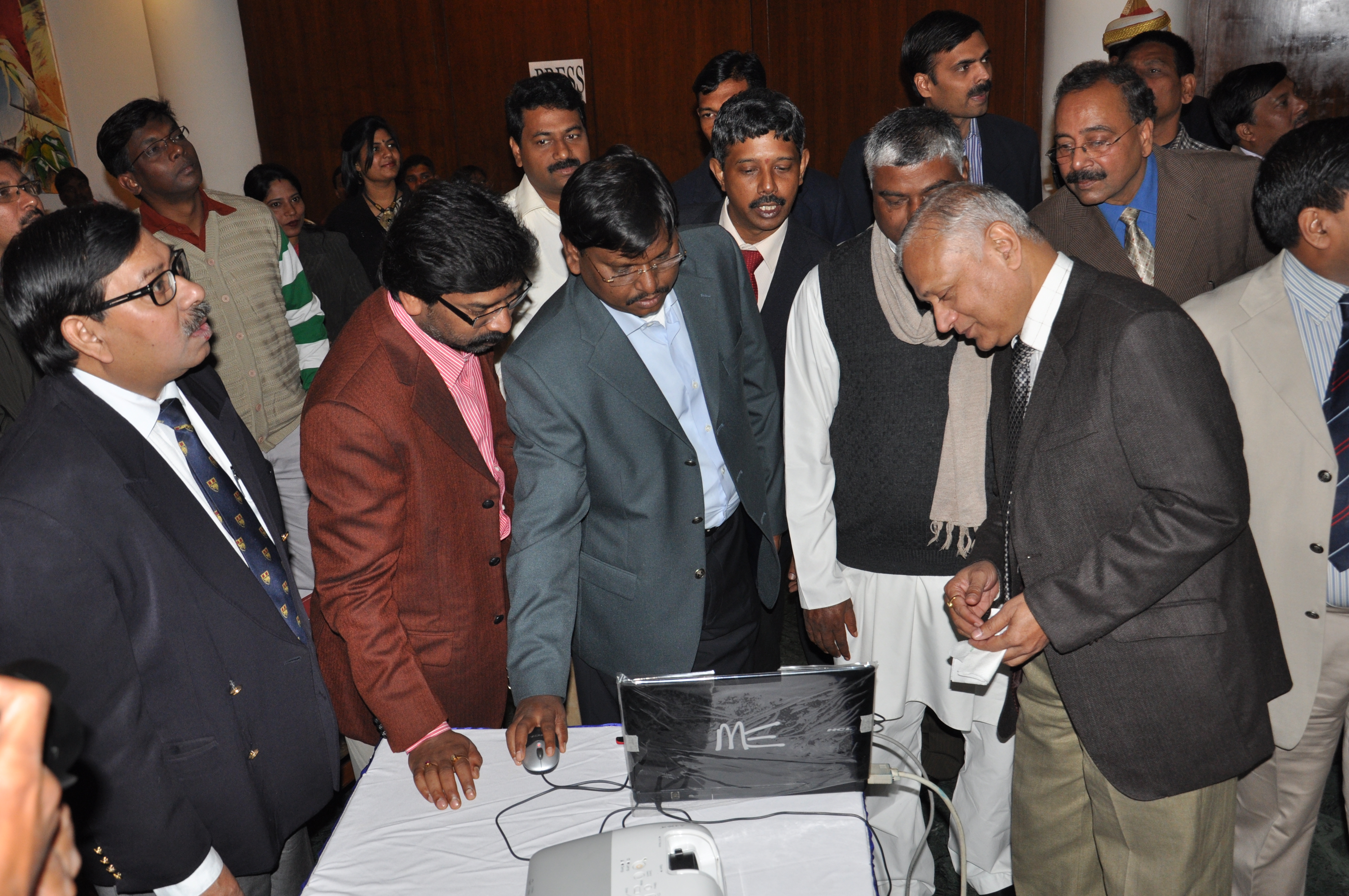
Shri Arjun Munda, Honorable Chief Minister, Jharkhand inaugurated the e-Procurement System of NIC (GePNIC) at Ranchi.
To bring transparency, efficiency, reduce tender cycle time and provide equal opportunity in the procurement process, the Jharkhand government took a landmark decision on 17th December ‘2010 by launching the Government e-Procurement System of NIC (GePNIC) at Ranchi. Speaking on the occasion...

 Subscribe
Subscribe




 Flipbook
Flipbook PDF (6.8 MB)
PDF (6.8 MB)